Cloud computing has enticed the IT landscape with a host of benefits. While productivity and profitability are one of the biggest USPs of cloud adoption, the enhanced accessibility and scalability are the flagbearers. The cloud tech has become an inevitable part of continuing business and is the key to unlocking organizational potential.
In the wake of the unprecedented global transition to cloud came the usual suspects – malicious actors endeavoring to ride the cloud bandwagon. The cloud’s ease of access has unwittingly sowed seeds for security challenges. Cybercriminals could compromise any cloud account if they ever gain the knowledge of the required credentials.
Vindicating the observation is the 2021 Ponemon Report, which stated that the frequency and severity of cloud account compromises are on the rise. The report titled ‘The Cost of Cloud Compromise and Shadow IT’ revealed some key findings about security risks in in the cloud, by surveying 662 IT security professionals in the US.
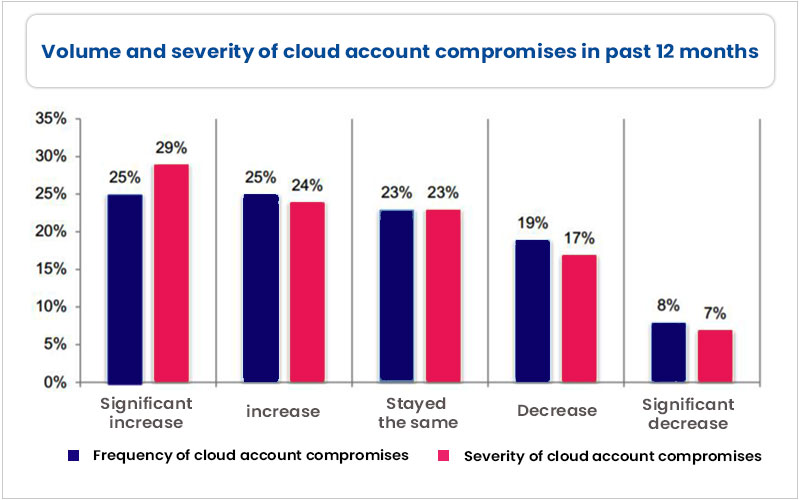
Of the respondents, 50% opined that the frequency or volume of cloud account compromises has increased significantly over the past 12 months. In addition, around 53% believed that the severity of cloud account compromises has burgeoned.
The grisliest finding in the survey was the cost of cloud account compromises. According to the report, the compromised cloud accounts inflict a financial loss of USD 6.2 million annually. The loss represents an average of 3.5% of the total revenues of surveyed organizations.
Reacting to the report’s findings, Dr. Larry Ponemon, Chairman and Founder of the Ponemon Institute, said, “This research illustrates that leaving cloud security in the hands of end-users or lines of business can be quite costly.”
“Cloud account compromises and sensitive information loss can disrupt business, damage brand reputation, and cost organizations millions annually,” he added.
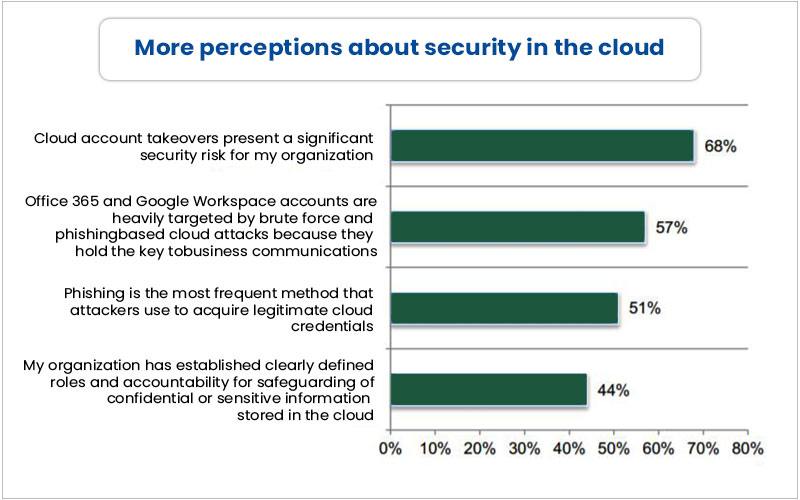
Moreover, 68% of the respondents mentioned compromised cloud accounts pose a significant security risk for their organizations. According to 51% of surveyed IT security experts, phishing is the most frequent method malicious actors use to acquire cloud account credentials.
Around 57% said that Microsoft Office 365 and Google Workspace accounts are significantly targeted by brute force and phishing attacks.
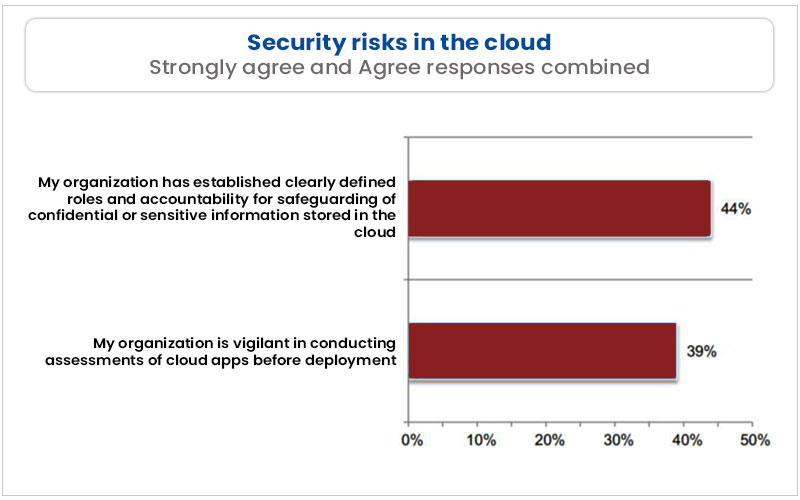
What’s more worrying is the finding that only 44% of organizations have clearly defined roles and accountability for safeguarding critical assets in the cloud. Only 39% of organizations are vigilant in conducting cloud application assessments before deployment.
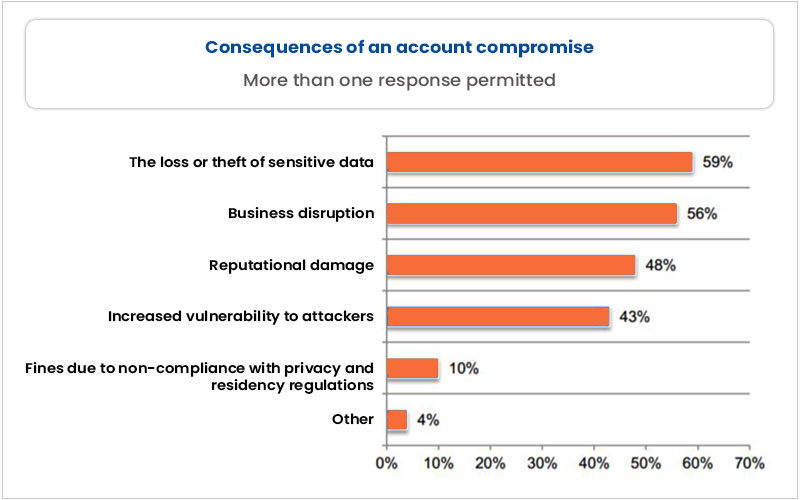
The report also revealed that highly sensitive data in the cloud is at risk. Around 67% of respondents reported that their company witnessed an account compromise that exposed sensitive data. The top three consequences of the account compromise are loss or theft of sensitive data (59%), business disruption (56%), and reputational damage (48%).
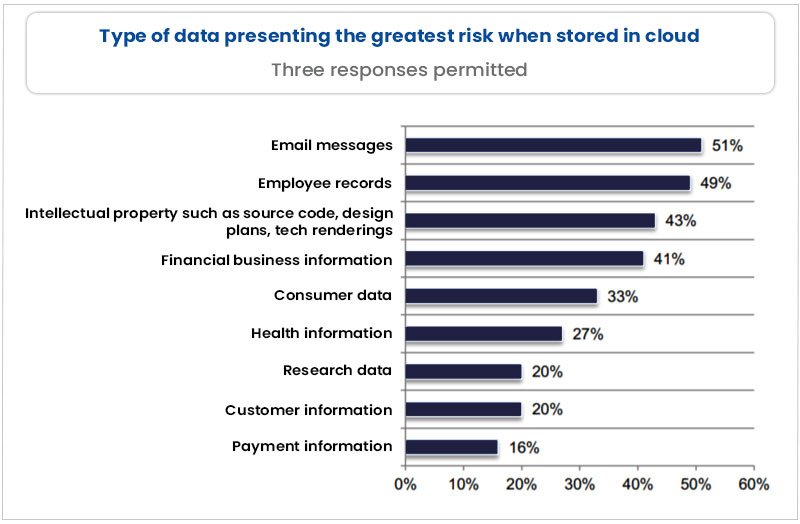
Additionally, email messages and employee records are believed to pose a greater security risk when stored in the cloud.
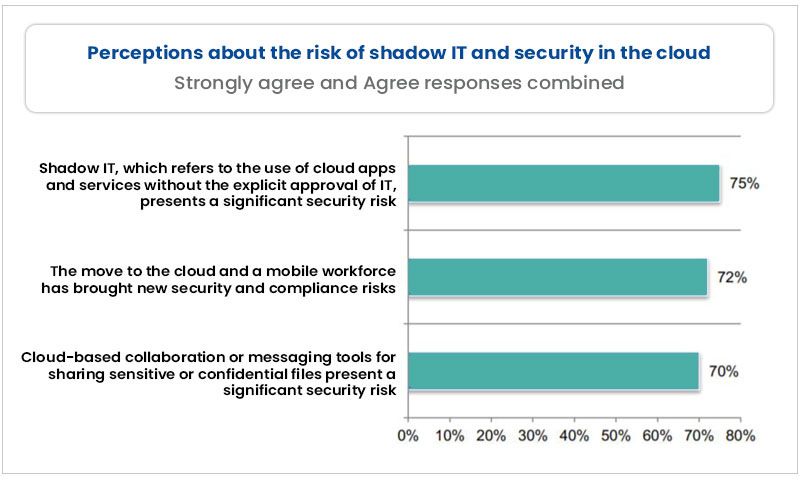
The report brought forth the impacts of shadow IT on the cloud – the use of cloud without approval from IT. In the survey, 75% of respondents strongly agreed that shadow IT poses a serious security risk to an organization. Around 72% believed that the cloud-based collaboration tools for sharing sensitive data present a significant security risk.
“The move to the cloud and increased collaboration requires a people-centric security strategy backed by a cloud access security broker (CASB) solution that is integrated with a larger cloud, email, and endpoint security portfolio,” said Tim Choi, VP of product marketing for Proofpoint.
“SaaS security cannot be an afterthought given the high cost of cloud account compromise,” he added.
More News Articles: