Containerization is undoubtedly a technological evolution that has effectively addressed the concerns of application delivery across organizations. DevOps consulting services play a crucial role in helping firms leverage containerization to its full potential.
Containers are known for their lightweight architecture, immutable nature in delivering apps, high-speed initiation, and execution abilities. While containers are most commonly termed as ‘advancement to Virtual Machines (VM),’ that’s not enough to start applying them. To truly benefit from containerization, companies often rely on a DevOps services company for guidance and best practices.
Effective container implementation demands a fresh mindset and a better understanding of its key principles, which DevOps consulting services can provide to ensure smooth integration and maximum impact.
Here are 9 important factors that you should pay special attention to in dealing with container services:
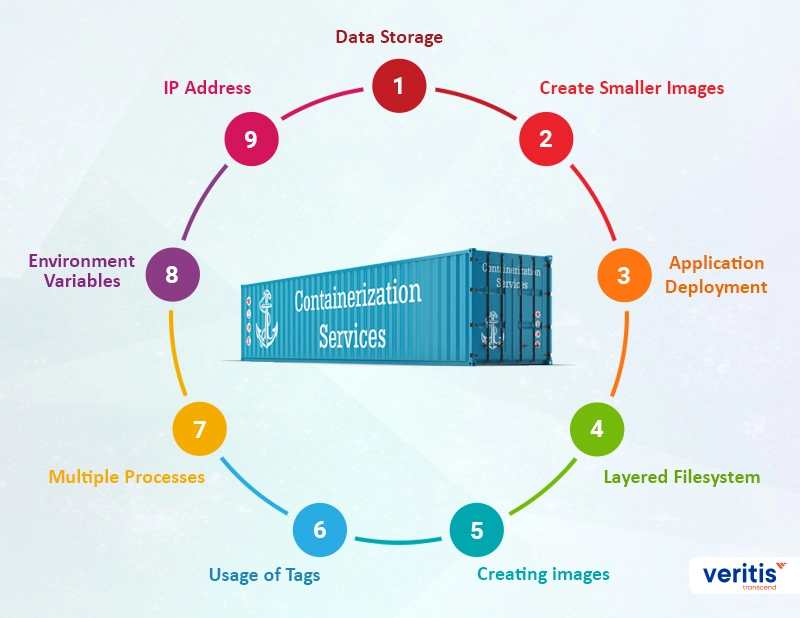
1) Data Storage
Data storage in containers doesn’t work as well as in traditional processes. Since the containers are flexible for updating, deleting, or replacing functions, any irregularities or improper data storage planning can lead to critical data loss. Experts recommend storing data in a volume while using containers to avoid such concerns.
Even in that case, ensure no two containers write data on the same volume to avoid data corruption. Shared data storage is the ideal option!
2) Create Smaller Images
Containers only carry files and library resources specific to individual applications/processes. Installing unnecessary packages or larger images that demand additional files can interrupt container services’ core ability to generate distributed applications.
3) Application Deployment
Owing to a few similarities with Virtual Machines, people tend to deploy applications in containers similar to VMs. However, application deployment in containerization cannot take place on running containers. That might work in the development phase, which involves continuous deployment and debug operations. However, applications should be part of the images for the continuous delivery pipeline involving QA and production.
4) Layered Filesystem
Using different layers instead of a single-layer image to effectively use a layered file system in containerization. Create a base image layer for the OS and individual layers for username definition, runtime installation, configuration, and application. This makes it easier to recreate, manage, and distribute images.
5) Creating Images
Experts recommend against using ‘docker commit’ for creating container images, owing to its limitations in generating images with reproducible ability. Instead, Dockerfile or any other source-to-image approach is highly recommendable. Storing images in a source control repository like Git allows you to track changes to Dockerfile.
6) Usage of Tags
The layered filesystem nature of containers allows tags to be used. However, the ‘Latest’ tag, similar to ‘Snapshot’ in Maven, is strictly not recommendable in containers. It does not mean the latest and is just a tag applied to a container image by default. Usage of this tag can lead to misunderstanding within functionality and result in retrieving the wrong ‘latest’ version from the build cache.
This can also create confusion when a new, backward-incompatible version replaces the parent layer, making the application dysfunctional.
7) Multiple Processes
Files and resources in every container package are limited only to the specific microservice for which the container is intended. Because of this, containers are best suited for running a single process (application server, database, or any other). Running multiple processes makes managing, retrieving logs, and updating processes individually challenging.
8) Environment Variables
In a container environment, storing credentials like username and password in a container image is not recommended. Instead, try to retrieve them from outside the container through environment variables.
9) IP Address
It’s not recommended to rely on IP addresses much in containers, as every container has its IP address that changes for every start or stop instance. This becomes a problem if an application or a microservice wants to communicate with another container on board. Instead, environment variables can be the best way to pass proper hostnames and switch between containers.
Practical Example: DevOps and Cloud Migration in Electronics Industry
Effective container implementation often goes hand-in-hand with broader IT modernization initiatives. Veritis recently partnered with a leading electronics manufacturer to implement DevOps-driven IT infrastructure modernization, migrating from virtual machines to cloud environments. This approach not only streamlined their operations but also enhanced scalability and deployment efficiency—key factors that resonate with container adoption strategies.
For a detailed look, check out the full case study: Implementing DevOps for IT Infra and VM to Cloud Migration in Electronics Industry.
On an End Note
Understanding the technical aspects behind it is more insightful and the best way to achieve success in a specific technology.
Wait no more! Get on to make the checklist for successful implementation of technology containers in your application ecosystem with expert DevOps consulting services to guide you through the process
[WPSM_AC id=13893]
Latest Stories: