Containers have gained popularity for their ability to offer applications agility, scalability, and portability. Because of this, they are often termed an alternative to traditional Virtual Machines (VMs)!
Containers have proven to significantly improve the application development speed, and ensure effective resource utilization and production efficiency.
There are many advantages that Containers show over VMs, such as:
- Convenient app packaging and less release overhead
- Short lifetimes that minimize the risks of outdated packages
- Less shift from the original state as the workloads run on short timeframes and can be rebuilt and re-pushed easily
Containerization vs Virtualization: Key Differences in Workload Management
Container application workloads differ from VMs in many ways. However, the most common discussion when comparing both is the ‘Security’ aspect, especially when considering containers vs. VM security.
Virtual machines were the way to go before containerization became popular if you needed to separate environments within a physical infrastructure. However, the focus on containers changed in 2013 when Docker Inc. unveiled its containerization software. Since then, containers have gained popularity, changing the cloud computing environment. In addition, containers’ agile development approach attracts an increasing number of engineers. Virtual machines and containers were both created with the concept of making the most of resources from an already existing physical infrastructure.
What are VMs or Virtual Machines?

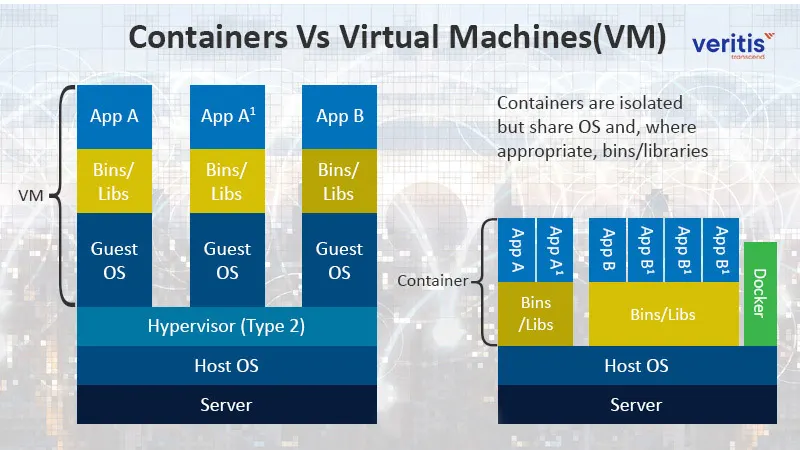
A virtual machine (VM) is an isolated environment that simulates a computer system with access to real hardware resources. The hypervisor software, which simulates the physical infrastructure and divides the resources into numerous virtual machines, runs on top of virtual machines. The host computer or virtual machine monitor is another name for the hypervisor.
Although a separate physical server supports each virtual machine, it appears they are all running on bare-metal hardware. VMs are usually oversized and many gigabytes in size since each VM container has its guest operating system, kernel, binaries, libraries, and applications.
What are Containers?
Containers virtualize the host operating system and run packaged applications on top of it to create isolated environments on a physical server. Unlike virtual machines, container applications virtualize the OS rather than the hardware. They are constructed over the host OS kernel and use the same libraries and binaries.
Only the application and its dependencies are packed in container technology because they share most of their requirements. They are merely megabytes in size and far lighter than virtual machines. To deploy a container-based application, you need two components: a platform for container application orchestration and a container-building tool like Docker and Amazon ECS.
There are numerous platforms for orchestration and containerization. The most popular configuration for complex applications is the combination of Google’s Kubernetes container orchestration platform and Docker, a platform for containerization. A master node, worker nodes, and pods make up container technology. The control that links your requirements with the rest of the system is a master node. Your containers are in pods and will deploy pods to worker nodes.
Containers vs Virtual Machines: Benefits and Trade-offs

Below we have listed some of the benefits of containers compared to traditional virtual machines:
1) Easy to Maintain
Because containers use a microservices-based architecture, your code is divided into manageable pieces that can be handled separately. As a result, you need not be concerned that updating or maintaining container virtualization will affect other parts of your application.
2) Portability
Containers are very portable when used as components of a distributed system. Moreover, it is simple to move containers around, even between environments like the public cloud, private cloud, hybrid cloud, multi-cloud, and bare-metal environments, because container technology compresses microservices and their dependencies in a small package.
3) Efficient Use of Resources
Most dependencies required to execute containers in cloud computing, such as an operating system, libraries, and frameworks, are shared by code bundled within containers. Unlike in virtual machines, there is just one copy of each relevant file in the hardware, which results in more efficient resource use. Additionally, since container virtualization is lighter, more containers in cloud computing can be placed inside physical server virtualization.
4) Highly Scalable
Platforms for container solutions orchestration were developed to assist you in managing your containers. Container orchestrators like Kubernetes or Docker Swarm automate scaling, networking, and deployment tasks. Applications that use containers are very scalable and can scale up and down quickly by adding new nodes and pods as necessary.
Container Cons
1) Runs a Single OS
This can be advantageous if you only use one operating system, but it is disadvantageous if you need to be able to use it on various operating systems. Lightweight virtual machines can be used to run an earlier version of the same operating system.
2) Insufficient security measures
Containers offer minimal separation from the host OS and other containers on the same machine. As a result, the security boundary is less robust than with virtual computers.
According to StackRox, however, experienced container based virtualization users are more concerned with security as they work to enhance communication between DevOps and Security.
Frequently Used Container Vendors:
- Mesos
- Docker
- RedHat Openshift
- Google Kubernetes Engine
- Linux Containers
- Windows Server Containers
Virtual Machines Pros
1) Can Simulate Numerous OS
You don’t need to purchase new hardware each time you require a different operating system because you can run whatever operating system you choose inside a virtual machine.
For instance, using a virtual machine saves you from purchasing multiple pieces of hardware when you need to mimic and test your applications across various operating systems to understand their capabilities better.
2) Additional Sources
A virtual machine is given access to many more resources than container solutions are. VMs are, therefore, more suited for resource-intensive tasks. VMs are preferable to containers in cloud computing for tasks with more significant file volumes and lengthy lifecycles.
Resource-intensive operations can be executed on containers. However, the cost of using containers rather than a VM container must be considered. Prepare your requirements in advance and conduct research to determine which choice will be more affordable for your application.
3) Hard Security Boundaries
Since you’re running a different operating system from the other machines on the same physical server virtualization, VMs increase the isolation level between nearby systems. In contrast, running within a single OS while using containers in cloud computing allows defects to damage the entire system.
Because of the complete isolation provided by VMs, security is improved, and vulnerabilities are more difficult to exploit. Virtual machines (VMs), which have a more assertive boundary, are preferred if you don’t have control over your environment.
Even so, top container based virtualization solutions providers are working harder to improve security over time, so you might soon see containers that are as secure as virtual machines.
Virtual Machines Cons
1) Harder to Keep the OS Updated
You must update and maintain each operating system independently because there are several in a single virtual machine. This is laborious and time-consuming, especially if you have several virtual machines.
2) Inefficient Use of Resources
Virtual machines frequently offer too many resources to run a single application.
However, once a VM is allocated to a resource, even though it requires less capacity, it takes up the entire space. If your planning is flawed, this results in idle power that you can employ in other ways.
In addition, VMs contain copies of the virtual hardware that the operating system needs, libraries, binaries, and other files. Repetitive files broadly use the servers’ RAM and CPU.
Frequently Used VM Vendors:
- KVM
- Xen
- VMware
- Hyper-V
- VirtualBox
Security in VM Perspective
Segmentation boundary is vital to the security of a VM environment. In a traditional virtualization environment, the boundary segment lies between different ‘virtual hosts’ and between ‘VMs and hypervisors.’ Thus, traditional VMs, such as a multi-tenant cloud, are preferred in areas that require firm segmentation boundaries.
This level of segmentation boundary is an excellent advantage if immediate changes are to be made to the underlying network configuration, which the teams can address through micro-segmentation at the network layer.
However, on the negative side, this security aspect might have some potential downsides in traditional VMs. Generation of undesired images on a larger scale and outdated images serialized on a disk are serious challenges that might arise with traditional VMs.
Security in Containers Perspective

Containers are often thought of as ensuring security boundaries like VMs. However, they may not guarantee this. Containerization vs. virtualization security lies under the control of a hypervisor below the level of the guest OS. In contrast, containers run on the same OS instance as the container engine. The unique aspect is that different containers running on the same instance interact neither among themselves nor with the container engine.
While instances stay longer in a traditional VM environment, container instances can be torn down and rebuilt whenever necessary for subsequent redeployments. This level of porous segmentation boundary in containers provides a security advantage and adds value to the broader microservices-based deployment model.
Traditional applications are not adequately isolated from each other within a VM, giving a malicious program scope to penetrate and control others. Conversely, containers run isolated from each other, each possessing its security level and remaining unharmed.
Outdated packages remain one of the most common vulnerabilities to applications running in VM.
In a container environment, microservices and CI/CD pipelines make releases more frequent and shorten workloads’ lifespans, thus minimizing vulnerability through outdated packages. Moreover, the container engine’s host OS is robust and gets updated automatically.
Overall, Containers enjoy the ‘security advantage’ because of their association with the CI/CD pipelines and DevOps services that allow regular releases and keep them updated all the time with regular patch updates.
In contrast, workloads on VMs will need administrators to manipulate them frequently to keep applications and OS updated, which can cause a drift in the application’s lifecycle’s original state.
Real-World Insight: DevOps Transformation in the Oil & Gas Sector
A leading oil and gas service provider partnered with Veritis to modernize its enterprise IT operations through a customized DevOps framework and containerized infrastructure. This strategic move enabled greater operational agility, improved security compliance, and more efficient management of complex systems—demonstrating how DevOps can deliver measurable value in high-stakes, regulated industries.
For a closer look, read the full case study: DevOps Enterprise Mgmt Support for Oil & Gas Service Provider.
Conclusion
Last but not least, VMware provides security and stability, which are essential for your production environment. However, numerous products are available to extend the functionality of Docker and VMware containers through automation, orchestration, and other features, often implemented through DevOps consulting services.
Now, it’s time to choose what your environment demands. With the right DevOps consulting services, you can ensure that your containerized environment is optimized for efficiency and scalability!
Need some assistance? Contact Us!
Related Stories:
- Key Containerization Benefits for Your IT Business
- Amazon Redshift Vs Azure Synapse Analytics: Difference Between Top Data Warehouses
- Top 10 DevOps Engineer Skills That Make A ‘Perfect’ DevOps Engineer
- Which Cloud has Better Private Connectivity: AWS or Azure or GCP?
- Azure DevOps Services for New-Age DevOps Professionals
- AWS vs Azure vs GCP: Breakdown of Cloud Migration Services (Infographic
- 7 Key Containerization Benefits for Your IT Business