
Table of contents
As businesses migrate to the cloud, cloud security automation becomes essential for safeguarding sensitive data and applications. Leveraging security automation allows companies to proactively defend against cyber threats in real time, improving their overall security posture. Veritis helps organizations implement cloud security automation strategies that ensure resilience and agility in the digital domain.
Although the cloud offers significant advantages, security concerns remain a critical barrier to adoption. A major hurdle has been automating cloud security infrastructure in complex hybrid and multi cloud environments. However, cloud automation can be a game changer. By automating security workflows, businesses can streamline the process of gathering critical information, allowing them to focus more on innovation and growth. At Veritis, we help companies adopt cloud security automation best practices, ensuring they maximize the benefits of cloud security automation while mitigating risks.
With 54% of organizations now using cloud service automation tools, the advantages are clear: improved security posture, cost reductions, and enhanced operational efficiency. Veritis’ approach to cloud security strategy automation focuses on automating tasks like configuration management, vulnerability scanning, and identity management. These benefits of cloud security automation reduce human errors, improve compliance, and enhance response times. Through automatic security processes, Veritis ensures businesses can confidently secure their cloud based assets in the face of evolving cyber threats.
Speak with an Cloud Security Expert
What is Cloud Security Automation?
Cloud security automation leverages advanced technology to optimize and strengthen an organization’s security operations. Utilizing software driven automation efficiently manages critical tasks such as threat detection, incident response, and vulnerability management. Automating these routine security processes enhances operational efficiency, minimizes response times, and reduces the risk of human error, ultimately improving overall cybersecurity resilience.
5 Steps for Successful Cloud Security Automation
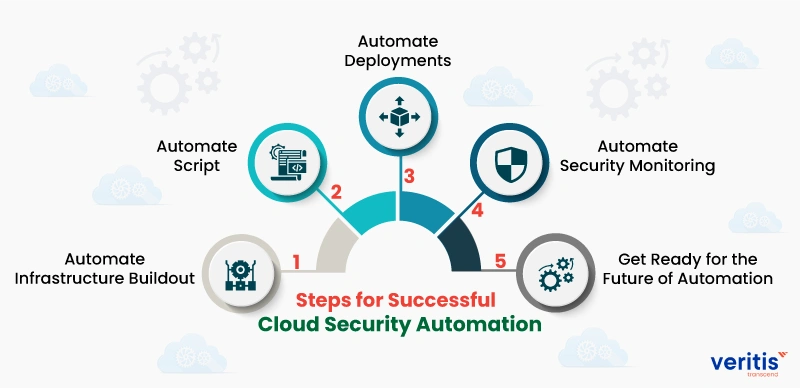
Here are five cloud security automation best practices for the successful implementation of cloud security automation:
1) Automate Infrastructure Buildout
By automating infrastructure buildout, engineers are relieved of manually configuring security groups, networks, user access, firewalls, DNS names, and log shipping, among other tasks. This significantly reduces the scope for engineers to make security mistakes.
Moreover, security team automation does not need to worry about cloud security automation best practices whenever it spins up a new instance, as it only has to touch the scripts, not the instances, to make the changes.
2) Automate Script
In traditional IT, a zero day vulnerability or any other major security workflow automation issue requires an organization’s system engineers to work rigorously to patch every server manually. However, automating scripts requires only a single line change in the manifests to ensure the newly released version is running instead.
These automation script resources are declarative management tools that automatically configure instances, virtualized servers, or even bare metal servers.
These scripts prepare a new instance for production whenever it is launched, including security configuration tasks such as ensuring central authentication, installing intrusion detection agents, and enabling multi factor authentication.
3) Automate Deployments
Automating deployments is one of the best practices in DevOps implementation, and it can also improve an organization’s security posture. In a zero day vulnerability, deployment automation ensures that changes to the DevOps tool script are automatically deployed across all instances or servers. This allows a single system engineer to respond quickly to automated threat detection.
4) Automate Security Monitoring
In the growing trend of hybrid and multi cloud environments that support individual applications, monitoring the entire infrastructure in a single interface is imperative. Automating security attacks and downtime can be resource intensive and time consuming; identifying and resolving the issue can be challenging.
Automated security monitoring provides engineers with the necessary intelligence to address threats and secure critical assets.
5) Get Ready for the Future of Automation
Data balloons and hybrid environments will become mainstream within the next few years, making the manual security approach incompetent. Hence, now is the best time to develop or outsource an internal automation team. Although achieving end to end process automation across hybrid environments may take months or even years, it will prove infinitely more valuable than training employees to reduce human error.
Useful Link: How Cloud Automation is Driving DevOps Efficiency?
5 Stages of Cloud Security Automation Framework
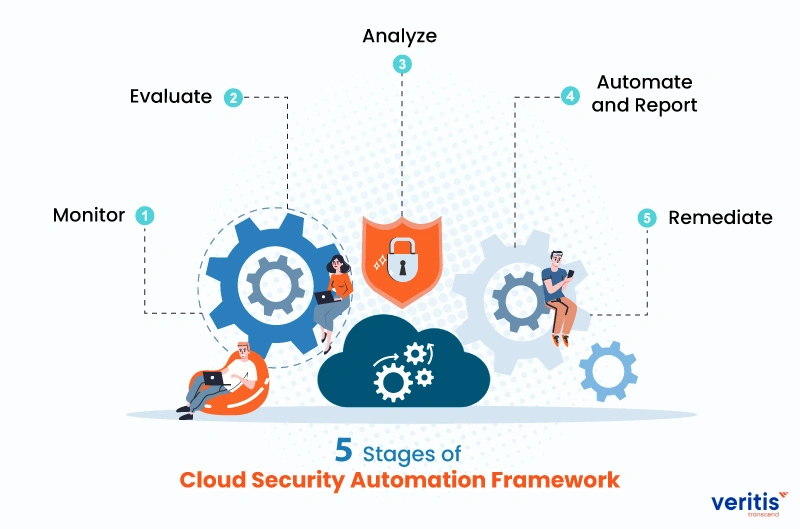
Automation of cloud security involves a 5 step strategy as follows:
1) Monitor
Your cloud capacity will always scale to meet all the operational needs. So, monitoring the workflow of all the tasks in your cloud security operations automation is imperative. This enables you to understand how each workflow is carried out.
2) Evaluate
The first critical step in automating cloud security infrastructure is knowing and prioritizing the tasks to automate. Closely monitoring workflows helps identify tasks that should be automated, such as repetitive tasks, automated cloud deployments, resource provisioning, and creating automation security rules.
3) Analyze
Analyze the collected information in depth, categorizing it based on its severity as low, medium, or high. Then, low risk processes are automated first, followed by medium and high risk processes. The in depth analysis also helps you control automation and study its impact on infrastructure.
4) Automate and Report
The resulting analysis can now be sent to integrated systems to automate the workflows. The automation processes are then configured to generate reports that give an overview of the changes before or after.
5) Remediate
By now, you will get a clear picture of cloud automation services, irrespective of whether you started automating simple or complex workflows. This enables you to implement remediation and enhance the overall automation security posture.
Useful Link: Cloud Infrastructure Automation: The Imperative for Cloud Success!
Benefits of Cloud Security Automation
Apart from the reduction of manual security tasks, let’s explore how the benefits of cloud security automation can further enhance and propel your best cloud security strategy services:
1) Accuracy
Human errors often cause misconfigurations. Implementing a consistent hardening process that maintains uniform configurations across development, quality assurance, and production settings not only simplifies the deployment of secure environments but also significantly reduces the likelihood of guesswork or human mistakes.
2) Speed
The rapid pace of infrastructure provisioning and the automated cloud deployment of cloud native applications can pose challenges. Often, the availability of resources within engineering and automating security teams becomes a bottleneck for automating security. This can lead to the automation of security tasks, causing delays or deferring subsequent releases. Automation comes to the rescue by enabling enterprises to automate configurations and manual processes. It also facilitates the integration of scans and testing right from the initial stages of development through automated cloud deployment.
3) Enhanced Security
Security automation is vital in safeguarding infrastructure and applications by identifying and promptly responding to threats, diminishing reliance on human intervention for monitoring and addressing vulnerabilities.
4) Compliance
Streamlining the automation of checks and reports empowers you to demonstrate compliance without hindering the development process or consuming significant engineering resources. This approach ensures compliance verification becomes an efficient and integrated part of the development lifecycle, allowing teams to concentrate on their core tasks and innovation rather than being bogged down by compliance related bottlenecks.
5) Scalability
When a process is automated, it gains the capability to operate autonomously in various locations and at any time, requiring minimal additional intervention. This enhanced level of flexibility and independence in automated processes can significantly contribute to efficiency and reduce the dependency on manual oversight, making operations more agile and responsive to dynamic demands.
A continuous, automated security protects your enterprise’s critical cloud automation assets from evolving threats, as well as helps your business reap the following more benefits:
- Consistency in security operations automation
- Reduced manual errors
- Advanced security measures
- Robust security posture
- Rapidly identify and address security gaps
Useful Link: What is Cloud Security Posture Management?
Best Practices for Cloud Security Automation

1) Automating Configuration Management
A key component of cloud security automation is ensuring that cloud environments are configured securely. Veritis offers cloud service automation tools that automate configuration management, fortifying your cloud security infrastructure against potential vulnerabilities. This proactive method forms the foundation of a reliable cloud security strategy automation.
2) Automated Vulnerability Scanning
Continuous monitoring is vital due to the increasing complexity of cloud environments. Veritis provides security automation through automated vulnerability scanning, helping businesses identify weaknesses before they can be exploited. This cloud security automation approach ensures that companies stay ahead of potential threats, providing substantial benefits of cloud security automation such as enhanced protection and peace of mind.
3) Identity and Access Management Automation
Controlling access to cloud systems is critical to maintaining a secure environment. Veritis helps businesses implement cloud automation for identity and access management (IAM), a key component of cloud security automation. By automating IAM, businesses can significantly reduce the potential for unauthorized access while ensuring that the right users gain access at the right times.
4) Automated Patch Management
Outdated systems pose a significant risk in cloud environments. Veritis provides cloud computing automation to ensure automatic and continuous patch management. Our automatic security solutions ensure that your systems stay up to date with the latest security patches, strengthening your cloud security strategy and preventing cyber threats from exploiting outdated software.
5) Log Monitoring and Analysis Automation
Log monitoring and analysis are crucial to identifying threats in real time. Veritis utilizes cloud security automation to streamline this process, enabling businesses to swiftly detect and respond to security threats. This cloud security automation ensures comprehensive monitoring, enabling faster decision making and bolstering your cloud security infrastructure.
Useful Link: 8 SaaS Security Best Practices to Secure Applications
Innovative Strategies for Cloud Security Automation

1) Automating Cloud Security Infrastructure for Robust Protection
A secure cloud security infrastructure is the foundation of a robust defense system. Veritis leverages cloud security automation to automate the deployment and management of security protocols, reducing vulnerabilities and ensuring continuous protection. This proactive approach offers significant benefits to cloud security, including more robust defenses against evolving cyber threats.
2) Automating Threat Response With a Cloud Security Strategy
An effective cloud security strategy requires automation in security processes to handle real time threats. Veritis uses cloud security automation to enable automated responses to security incidents, ensuring businesses stay ahead of threats. Organizations can benefit from rapid detection and response by integrating cloud automation, minimizing potential damage.
3) Streamlining Identity Management With Cloud Security Automation
Automating identity and access management (IAM) is critical to safeguarding cloud environments. Veritis offers cloud service automation to handle IAM, preventing unauthorized access and maintaining automatic security across cloud platforms. This fundamental aspect of cloud security automation ensures businesses can securely control system access.
4) Enhancing Patch Management Through Cloud Automation
Outdated systems are a common security risk. Veritis employs cloud automation to automate patch management, ensuring all software is current. This continuous approach to patching improves security by eliminating vulnerabilities, demonstrating one of the core benefits of cloud security automation in maintaining secure, resilient systems.
5) Real time Threat Detection With Automated Log Monitoring
Veritis enhances security by automating log monitoring and analysis, enabling real time detection of potential threats. This cloud security strategy improves operational security by providing early warnings of attacks. Through cloud security automation, businesses benefit from faster decision making and a more secure cloud security infrastructure.
Case Study: Infrastructure Automation & Orchestration for a Major Airline
A leading airline with complex hybrid cloud operations faced delays, manual configuration drift, and operational inefficiencies across its IT stack. The relief from these operational inefficiencies was a significant benefit they experienced after engaging Veritis to automate and orchestrate their entire cloud infrastructure, maintaining competitive agility and reliability.
Challenge:
The airline operated multiple environments (public and private cloud, on prem), relying on manual provisioning and inconsistent configurations. This led to deployment delays, higher operational risk, and challenges with scaling.
Veritis’ Solution:
Veritis rolled out a unified automation framework using Ansible and cloud security orchestration tooling to:
- Automate provisioning and configuration for compute, network, and security components
- Standardize deployments across environments
- Integrate CI/CD pipelines for infra changes and application delivery
Impact:
- Faster Deployments: Reduced provisioning time from days to minutes
- Consistent Environments: Elimination of configuration drift and manual errors
- Operational Resilience: Improved uptime and reliability during changes
- Scalability: Enabled rapid scaling to support high demand flight and operational loads
This project demonstrates how infrastructure automation can significantly enhance agility, efficiency, and operational maturity in mission critical airline IT systems.
Read the complete case study: Infrastructure Automation & Orchestration for Airline Enterprise Public Cloud.
Conclusion
Cloud security automation certainly has a lot to prove to your business with numerous invaluable benefits; however, it should also be noted that it may be a more complicated and expensive process than not involving automation in a security program. Technology solutions often require significant stacked costs, and the implementation timeframe is substantial. On the contrary, security automation must also require high level expertise in effectively setting and maintaining security operation automation.
With all these issues, though, it makes good sense to consider having a reputed cloud consulting services like Veritis in these cloud systems as you transition to or continue to run in the cloud. Veritis has been securing enterprise cloud solutions for over 20 years, with many Fortune 500 and emerging companies relying on their cloud and infrastructure services. Being a team of AWS, Azure, and GCP certified cloud consultants, we assure you that your cloud security automation will be set up effectively and efficiently.
Veritis has been honored with prestigious awards, such as the Stevie and Globee Business Awards, demonstrating its significance in the realm of excellence. Our clients have a 100% satisfaction rate, a measure of our trust and dedication to 100% quality solutions. For new organizations transitioning to the cloud or those seeking to optimize their existing cloud infrastructure, Veritis offers solutions to meet your expectations for securely thriving enterprises in the cloud era.