
In today’s digital world, the ability to deliver applications at the pace of business has become essential. Thankfully, DevOps has made this possible by bringing together business, Dev, and Ops teams and applying automated processes to streamline the application development lifecycle.
However, secure application development has become challenging for enterprises as DevOps, and security processes are often disjointed. While organizations are wading through DevOps for more rigorous application development, security is often ignored.
Moreover, ensuring application security often resides with the security team, and most issues are identified only during the testing phase. This approach can’t keep up with the releases without halting the development process. The lag would spawn time-to-market delays, developer underutilization, and vulnerability backlog.
Cognizant of this DevOps security conundrum, many forward-thinking companies are turning to DevSecOps methodologies that help integrate security into the application development lifecycle.
Schedule a Call with DevSecOps Expert
Also Read: 14 Statistics That Shed Light Upon DevSecOps’ Opportunities and Challenges!
DevSecOps – Fine-tuning Application Security
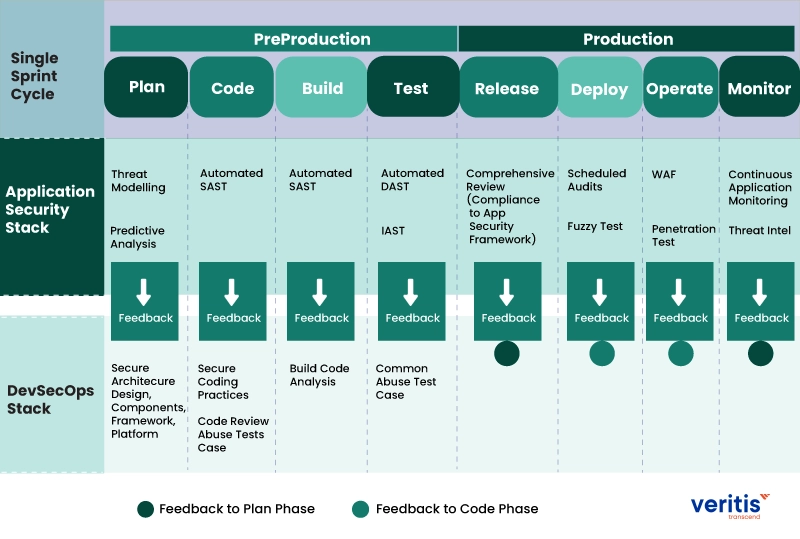
DevSecOps enables organizations to build a continuous application security process that fuses effectively with DevOps process. Security would be strategically deployed at every step of the software development lifecycle (SDLC).
DevSecOps methodologies empower enterprises with ‘shift-left’ practices to incorporate security measures early into the SDLC. This helps detect app security defects early in the SDLC, enabling DevOps teams to fix software vulnerabilities swiftly and effectively.
Also Read: What are the best DevSecOps practices for security and balance agility?
Let’s delve into the details on how to weave security into the application development lifecycle:
Boosting Continuous Application Security with DevSecOps
Organizations must incorporate security throughout the application development lifecycle, during development, testing, and production. However, the security integration must be seamless enough to avoid undesired friction in DevOps workflow and continuous integration/continuous deployment (CI/CD) processes.
There is a multitude of ways to integrate continuous application security. Here are six critical considerations for effectively integrating automated security testing across the development lifecycle:
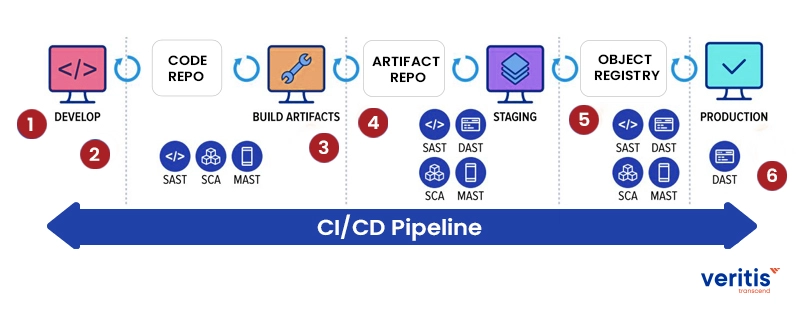
- Design Review: Rope in security when business objectives are being drafted along with backlogs and sprints.
- Code Review: Empower development and operations teams with security aspects. Create a secure coding checklist/template to help developers identify common and recurring issues.
- Pre-commit or Pull Requests: Implement Static Application Security Testing (SAST) and Software Composition Analysis (SCA) during the pre-commit or pull requests. This will help discover code issues.
- QA Integration: Implement SAST and SCA processes and Dynamic Application Security Testing (DAST) during the QA stage. This enables the DevOps team to identify high-certainty and high-severity vulnerabilities.
- Production Acceptance: Deploy DAST at this stage to discover potential production vulnerabilities. SAST and SCA will also be needed during this stage.
- Production: Continue the testing process with production-safe DAST even upon release. Production-safe DAST empowers DevOps teams to identify production vulnerabilities without impeding application performance. Moreover, protective technologies such as a web application firewall (WAF) and runtime application self-protection (RASP) must be implemented to secure running applications.
Integrating SAST into the application development lifecycle helps organizations realize potential benefits. According to a WhiteHat survey, enterprises realized a 25 percent reduction in time-to-fix after implementing SAST.
Also Read: DevSecOps – A DevOps Savior to ‘Cybersecurity’ Challenge!
When SAST was integrated with DAST, organizations witnessed a 50% downtick in new production vulnerabilities compared to implementing DAST alone. To achieve a cost-effective application security program, it is wise to implement all six integration points mentioned above via automation.
While it’s possible to build DevSecOps capabilities from scratch, a faster and more cost-effective approach is to partner with a third-party DevSecOps consulting services provider like Veritis. Partnering with Veritis helps establish a holistic security approach by incorporating innovations and technology trends.
Veritis DevSecOps framework enables shared responsibility among the development, operations, and security teams. Our DevSecOps strategy integrates security processes and tools that drive visibility, collaboration, automation, and agility into each phase of the DevOps pipeline.
Case Study: Marketing Solutions Provider Adopts DevOps
Veritis partnered with a top-tier marketing solutions firm to accelerate digital campaign delivery and strengthen application security.
Challenge
- Manual release processes and fragmented toolchains caused delays and inconsistencies
- Security checks occurred late, exposing campaigns to last-minute vulnerabilities
Solution
- Established a centralized DevOps practice to align development, operations, and security
- Implemented automated CI/CD pipelines with Jenkins, Ansible, and Infrastructure as Code
- Integrated early security scans (SAST/DAST) into build workflows
- Unified GitHub, Jira, Artifactory/Nexus, and Docker for seamless collaboration
Outcomes
- 3× faster release cadence with predictable, repeatable deployments
- 70% reduction in manual handoffs and errors
- Proactive security validation eliminated critical vulnerabilities before production
- Enhanced team productivity and continuous compliance reporting
Read the complete case study: Marketing Solutions Provider Adopts DevOps.
Let’s join forces to build, deploy, and iterate applications securely everywhere.
More Articles: