
Security architects are an essential presence in every IT department. But if any firm hasn’t embraced it, it’s time to adopt the DevSecOps culture in their workflow. DevSecOps is a trending software development methodology that involves DevOps and security. Similar to SecOps or DevOps, It is a concept that combines two separate teams into a unified environment. It is responsible for providing conditions for continuous secure software development.
What is DevSecOps? It is a strategic approach that integrates security practices into the DevOps pipeline, ensuring that security is not an afterthought but an integral part of the development process. DevSecOps was created to emphasize security automation and IT operations in the SDLC as a new concept in the IT field. It includes security as part of the DevOps foundation and is involved in every phase of the SDLC. It emphasizes software security throughout the software delivery process while delivering products faster than the traditional process.
The DevOps model is a new approach to creating software products that use agility, CI, and CD. Unlike the traditional software development process, where a security team joins only after a product is finished, the DevOps model integrates security throughout software development.
According to the report by the GitLab ‘2021, Global DevSecOps Survey’ found that there are dramatic advances in automation, security postures, continuous deployments, and release cadences. Nearly 4300 professionals shared their opinions that 25% of respondents were willing to have complete test automation. 60% of developers release code 2x higher performance and speed than ever.
Before delving into the topic, let’s explore DevSecOps, how it works, and its pros and cons.
About DevSecOps Services

The DevSecOps movement started in 1976 and continues to rise on the IT industry’s radar. The SDLC process has experienced a significant makeover in the last two decades. It mainly aims to deliver quality software in less time. This radical overhaul includes adopting tools, techniques, and DevOps principles. However, rapid software development has a higher risk of developing insecure code, so it further develops the DevOps principles to include security in their process, i.e., DevSecOps services.
DevOps applications have exploded in size and speed. However, they lack compliance and robust security. For this reason, the DevSecOps concept was introduced into the SDLC to combine development, operations, and security under one roof. Like DevOps, its security concerns automation, culture, and shared responsibility. The security operation aims to release better software quickly and detect software problems in production.
The main reason for involving security in the DevOps approach is to ease security issues in the last stages of the SDLC. DevSecOps boosts automation and involves security in the design, testing, planning, development, and monitoring. A few years back, a security team would add security to software towards the end of the development cycle, and a quality assurance team would test it.
Useful link: All You Need to Know About DevSecOps and its Implementation
DevSecOps Engineer is responsible for securing software development and identifying security threats.
Their job is similar to IT security professional roles. The top skills required for engineers are:
- Good communication skills
- Strong collaborating skills
- Good understanding of DevOps tools
- The person should know threats, compliance laws, and threat modeling tools.
- IT pros should know automated code analysis to detect threats and fix vulnerabilities.
- The IT pro should be familiar with Ansible, deployment systems tools like Hibernates, and developer tools like GitHub. He should also be familiar with programming languages like Java and PHP.
Adoption of DevSecOps
The following principles are adopted by DevSecOps engineers as follows:
- The first phase is planning, where engineers strategically prepare and aim for successful adoption.
- The next is the development phase, where the team’s engineer gathers valuable resources to provide guidance and set up a code review procedure to improve uniformity.
- The next step is the building phase; the source code involves machine code through tools.
- In the testing phase, the automated testing framework is subjected to multiple testing practices in the pipeline.
- In the following phase, engineers run IaC tools to automate the process and accelerate software delivery.
- The following phase is operation, one of the essential processes, and operation teams frequently engage in periodic maintenance.
- The scaling phase is one of the crucial steps in which IT engineers ensure that companies do not waste their resources to preserve big data centers.
Useful link: DevSecOps – For Bankers With Futuristic Vision
How does DevSecOps work?
DevSecOps workflow follows the following steps:
- First, the version control system is used for development.
- Team member assesses the application changes. The employee does this by addressing security issues, code quality, and potential flaws. The application is then deployed within security configurations.
- The application is tested in integration, user interface, back end, and security using test automation.
- The application moves to production if it successfully passes the test.
- Security software and multiple monitoring programs monitor the application in production.
Benefits of DevSecOps

It can ensure an application is stable and less vulnerable to malicious attacks. This concept has two essential benefits: security and speed. Numerous features of DevSecOps services benefit businesses of all sizes.
1) Better communication and collaboration between teams
This DevSecOps Security solutions culture promotes collaboration and teamwork among IT professionals with multiple skills and competencies to accomplish one goal. One of DevSecOps’ primary goals is to integrate teams.
2) Improve the agility and speed of development teams
Team members are under pressure to respond quickly, review, and fix vulnerabilities and other software issues while in the ongoing development process.
3) Improves better quality control and threat exposure
Although the DevOps team may see the security team as a source of delay, this shouldn’t be the case. Issues are detected and finished immediately before the entire project is completed. This DevSecOps strategy ultimately leads to better quality control procedures and shorter time projects.
Useful link: DevSecOps Security – The DevOps Answer to Cybersecurity Challenges
4) Enables early detection of software flaws
One of the security team’s main tasks is to manage and reduce risks effectively. This can only be improved by including the security team in the DevSecOps process, which can efficiently combine a product’s speed and reliability.
5) Provides better and quick response to changing client requirements
DevSecOps can work faster in reviewing projects, scanning vulnerabilities, and integrating changes and applications during development.
Drawbacks of DevSecOps
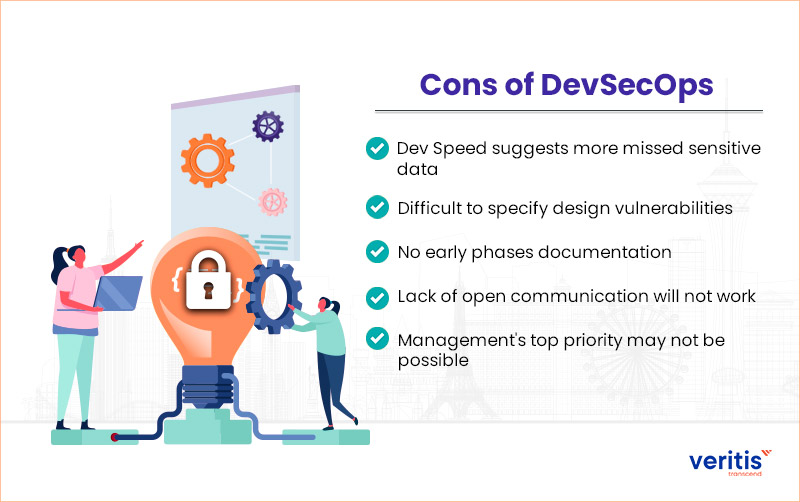
DevSecOps Challenges mean that DevSecOps can’t solve all business issues, and every organization must carefully evaluate its requirements and needs.
The below mentioned are some of the disadvantages of DevSecOps:
1) Dev Speed suggests more missed sensitive data
The DevSecOps approach has sped up the application’s development at the starting stage. However, this speed comes at the price of missing vulnerabilities.
2) Difficult to specify design vulnerabilities
This model depends on the agile system. It uses multiple techniques to produce the first application as soon as possible. This is because it is based on client feedback to improve the application. So, finding design based exposures becomes complicated and time consuming.
3) No early phase documentation
The absence of documentation in the beginning phase of application development makes identifying exposures, particularly the business logic ones, more complex, as security experts will require more time to understand the application logic.
Useful link: Signs of a Failed DevSecOps Strategy Which None Should Ignore
4) Lack of open communication will not work
Communication and collaboration are the two essential steps of the IT department; software development and security must be developed to work. However, if any of these teams withhold crucial information from each other, it may not work correctly.
5) Management’s top priority may not be possible
Not every software company executive views security as a top priority. As a result, an organization executive may not accept the changes a manager tracks. The business may only resume security testing once the software development processes are complete.
Case Study: Telecom Multinational Company Adopts DevOps
Veritis collaborated with a leading global telecom operator to unify and accelerate software delivery across mobile, broadband, video, and data services.
Challenge
- Fragmented toolchains and manual processes delayed releases and increased risk
- Security and compliance checks were reactive, leading to production vulnerabilities
Solution
- Established a centralized DevOps Center of Excellence to align development, operations, and security
- Implemented automated CI/CD pipelines with Jenkins, Puppet, Ansible, and Infrastructure as Code
- Embedded early security and compliance scans into each build
- Standardized toolchain integration across Bitbucket, Maven, JIRA, and Docker
Outcomes
- 2× faster release cadence with predictable, repeatable deployments
- 60% reduction in manual effort and handoffs
- Proactive security validation ensured compliance and minimized risks
Read the complete case study: Telecom Multinational Company Embraces DevOps.
Conclusion
DevSecOps is a new security model that involves security in the early stages of software development. It can ensure full functionality, reduce cyber threats, and accelerate software product deployment. Implementing security at every stage of the SDLC allows software products to be delivered quickly. This security solution can be implemented in the automotive, healthcare, finance, and retail industries.
It is a management model that involves security, operations, application development, and IaaS in a continuous delivery cycle. DevSecOps aims to apply security at all stages of the SDLC. This allows for continuous integration, reduced cost compliance, and quick delivery of software products. Its main objective is to make everyone responsible for security.
For over a decade, Veritis, the Stevie Award winner, has been a trusted partner for small to large companies, including Fortune 500 companies. We have enough expertise to deliver solutions for IT projects and combine emerging technologies in a dynamic environment. Veritis offers multiple technology services for your business with a cost effective solution. So, contact us to embrace productivity with the best DevSecOps tools.
Schedule A Call With DevSecOps Consultant
Additional Resources: