
In today’s IT world, few companies have yet to figure out how to secure the cloud effectively. As a result, there is a shortage of cloud security knowledge and legacy security regulations that do not cover the cloud.
Security must be adopted at every stage of the DevOps life cycle, known as DevSecOps. A company that runs cloud technology should adopt this approach, which requires policies, procedures, and new security guidelines.
By 2027, the global DevSecOps industry will have grown ninefold, to more than USD 17 billion, up from just over USD 2 billion in 2019.
Users with substantial app and software development exposure are familiar with DevOps. But do they know about DevSecOps, the combination of DevOps and security?
Before going in depth about the topic, let’s explore the concepts first. What is DevSecOps? Why is DevSecOps important, adopting and measures?
What is DevSecOps? DevSecOps is a security issue for the development and operations teams. It’s an automation, culture, and platform design model that involves security as a shared responsibility throughout the IT life cycle. It is an application security (AppSec) technique that involves security in the software development life cycle (SDLC).
DevSecOps should include security across the SDLC so that DevOps teams can deliver secure apps quickly and with high quality. In addition, CI/CD workflow, such as testing and risk mitigation, reduces the time consuming and expensive consequences of making patches post production.
DevSecOps has always been ideal for building security as an integral part of an app’s life cycle. It means building security into application development from start to end. It is an essential evolution in how development companies approach security.
With real time monitoring of loops and insights, DevSecOps spans the whole SDLC from planning and design to coding.
Useful link: DevSecOps Process, Benefits, Tools and Implementation
To adopt DevSecOps, teams should follow the below steps:
- To reduce software code attacks, security must be included throughout the SLDC.
- Assign some security practices to the DevOps team.
- Allow automatic security checks at each stage of the SLDC to combine tools, processes, and security controls through the DevOps workflow.
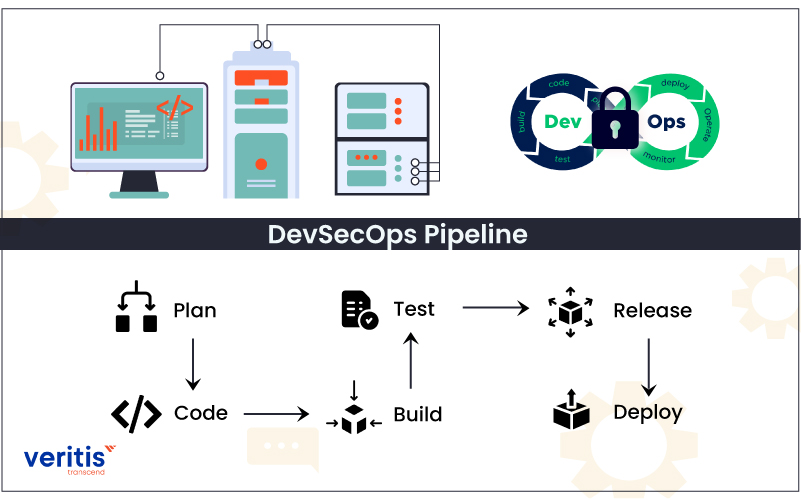
Security should apply at each stage of the DevOps pipeline, including plan, code, build, test, release, and deploy.
1) Plan
The DevSecOps plan stage is the least automated, comprising discussion, review, collaboration, and strategy of security analysis approach. Teams should execute a security analysis and develop a plan outlining where, how, and when security testing will happen.
The IriusRisk tool is the most popular DevSecOps planning tool and a collaborative design platform for threat modeling. Jira is used for issue tracking and management, while Slack supports software communication and team collaboration. All these tools are commonly used as add ons to support the DevSecOps strategy.
2) Code
Developers can run DevSecOps in the code phase to guide them in writing better secure programs. Code phase security practices include pre commit hooks, static code analysis, and code reviews.
Security technologies are involved in developers’ existing Git workflow. A security test automates triggers for every commit and merge. It even supports combined development and programming languages. The most popular security code tools are CheckStyle, PMD, Gerrit, Phabricator, Find Security Bugs, and SpotBugs.
3) Build
The build process starts when developers add code to the source repository. It aims to create tools to automate the security analysis of build output artifacts. Security approaches include unit tests, software component analysis, and static application software testing (SAST). In addition, it can add tools to an existing CI/CD pipeline to automate these tests.
Checkmarx, SourceClear, OWASP Dependency Check, SonarQube, Snyk, and Retire.js are for the build phase tools.
Useful link: DevSecOps – A DevOps Savior to ‘Cybersecurity’ Challenge!
4) Test
The test phase starts after a build artifact is built and deployed to testing conditions or staging. Executing a complete test suite requires a significant amount of time. Therefore, this phase should fail quickly to complete the more costly test jobs later.
During the test phase, DAST tools detect actual application flows such as SQL injection, authorization, user authentication, API related endpoints, and SQL injection. Multiple paid testing and open source tools are available in the current market, including Gauntlet, Arachi, Boofuzz, JBroFuzz, BDD Automated Security Tests, Owasp Zap, SecApp suite, and IBM AppScan.
5) Release
Test the application and executable code when the DevSecOps cycle reaches the release phase. The phase explores the configuration variables such as network firewall access, personal data management, and user access control to secure the runtime architecture.
Configuration management technologies are essential for security during the release phase. It allows visibility into the static configuration of a dynamic environment. Terraform, Puppet, Chef, Ansible, and Docker are configuration management tools.
6) Deploy
It’s time to deploy the build artifact to production if the preceding devsecops phases were successful. The only security issues to address during the deployment phase are against the live production system. Production TLS and DRM certificates should be checked and assessed for impending renewal.
Useful link: What are the best DevSecOps practices for security and balance agility?
Why is DevSecOps becoming essential?
DevSecOps combines security into the SDLC earlier. As a result, it is easier and less expensive to discover and patch vulnerabilities before they go too far into production. When development groups code with security from the start, companies across multiple industries can adopt DevSecOps to break through boundaries between development, security, and operations. It allows them to deploy more secure software faster.
Companies might ignore security measures for speed, but this experiment could backfire disastrously. Do you want to risk jeopardizing your latest app launch, especially if the launch’s success is critical to your company’s survival? There is also the possibility that a wave of security concerns emerges after the product is released, resulting in frustrated customers, many of whom may abandon your product and organization.
IT security is a significant concern in today’s digital world, and the threats are not going away anytime soon. Cyber attacks and fraud are becoming more common. With this harsh reality in mind, it is impossible for any enterprise today to ignore DevSecOps Security as a core part of the DevOps process.
Useful link: DevSecOps Solution to Cloud Security Challenge
Challenges of DevOps security
- Security is observed as a problem by DevOps teams
- IT security teams are unable to keep up with DevOps’ speed
- Most inexperienced tools and open sources have security flaws
- More attack opportunities emerge as a result of inadequately managed privileged access controls
Adopting DevSecOps measures
To successfully adopt DevSecOps in a strategy summed up as “moving security focus to the left,” the team must ensure that security is embedded into the program development from starting to end. Below are five crucial components of any DevSecOps model are:
1) Compliance monitoring
Stay compliant at all times to be ready for an audit. Integrated compliance monitoring provides a framework for accomplishing. It allows teams to work more quickly while maintaining traceability and more reliable controls.
2) Code analysis
Deliver code in small chunks to make it easy to discover faults quickly. Of course, the business will always need to perform code analysis. First, however, the functionality must be ingrained into the tooling developers use while pushing, merging, pulling, writing, and integrating lines of code.
Useful link: Achieving Continuous Application Security with DevSecOps
3) Change management
Any team can submit changes and decide whether they benefit or trouble the team. Change management is associated with bureaucracy in IT businesses.
4) Threat investigation
Identify threats as they emerge in each code to change and update quickly. Threat investigation is one crucial security practice used to guide and visualize the potential of something awful.
Case Study: DevSecOps Implementation for an Energy Services Firm
Veritis partnered with a global energy services provider to embed security across their development pipeline and accelerate regulatory compliance.
Challenge
- Manual, late stage security reviews led to undetected vulnerabilities and audit delays
- Development, security, and operations teams operated in silos, slowing time to market
Solution
- Integrated SAST (SonarQube) and automated DAST into CI/CD workflows
- Employed Ansible Infrastructure as Code to enforce consistent security configurations
- Unified GitHub, Jira, Artifactory/Nexus, and Docker toolchains for seamless Dev–Sec–Ops collaboration
- Delivered “security by design” training to align cross functional teams
Outcomes
- Automated security gates eliminated manual handoffs
- Early vulnerability detection cut production incidents by over 70%
- Release cadence improved by 50% with on demand, compliant environments
- Continuous compliance reporting met stringent industry regulations
Read the complete case study: DevSecOps Implementation: Enhancing Security for an Energy Services Firm.
Final Thoughts on DevSecOps

More development teams modernize their processes and use new tools but must maintain high security. This cyclical process should regularly be iterated and applied to new code deployments. Hackers and exploits constantly change, so modern software teams must keep up.
Moreover, Enterprises will adopt DevSecOps services more as the process becomes more automated. DevSecOps deployment becomes a no brainer when automation is combined with high security.
Veritis, the Stevie Awards winner, has been a trusted partner for Fortune 500 companies, including emerging companies; we have enough expertise to offer the best solutions for your business.
So, reach out to Veritis and walk away with the best DevSecOps tools and cost effective solutions.
Explore DevSecOps Services Got Questions? Schedule A Call
Additional Resources: