
Traditional software delivery often treats quality and security as end of pipeline concerns, waiting until the final stages to test, scan, and validate code. Shift left DevOps (or DevOps shift left) overturns this model by embedding validation earlier in the development lifecycle.
This shift left methodology and shift left approach in DevOps answer the question, “what is shift left approach?” by moving automated tests and security checks into the design and requirements phases. By shifting left in DevOps and adopting a robust left shift strategy, teams drive shift left development, leveraging modern shift left technology to catch defects before they ever reach staging. Embracing DevSecOps shift left and a proactive shift left security DevOps stance ensures continuous compliance and quality.
- The shift left DevOps approach embeds testing, security (SAST, DAST, IAST, RASP), and compliance checks early in the CI/CD pipeline, delivering a cohesive shift left strategy that fortifies pipelines from commit through deployment.
- Early validation is core to shifting left in DevOps, provides faster feedback loops, boosts deployment frequency by up to 40%, and realizes 7–10× lower remediation costs, balancing speed with security.
- Core shift left methodologies, including automated unit/integration testing, dependency and container scanning, policy as code, and CSPM, operationalize your shift left approach in DevOps, accelerating delivery and minimizing risk.
- A phased roadmap (Assess, Plan, Pilot, Scale, Optimize) combined with standardized tooling and cross functional collaboration ensures successful shift left development and sustained innovation under a unified shift left security approach.
By partnering with Veritis, a proven leader in shift left DevOps transformation and DevOps consulting services, you gain experts in shift left technology who seamlessly integrate SAST, DAST, IAST, RASP, CSPM, and automated testing frameworks into your CI/CD pipelines. We guide you through every phase: Assess, Plan, Pilot, Scale, Optimize, to deliver rapid ROI, foster a culture of quality and security, and transform your delivery engine into a strategic growth driver with Veritis’ signature left shift strategy.
What is Shift Left DevOps?

At its core, shift left DevOps, also known as DevOps shift left, redefines traditional delivery by moving validation, testing, security scans, and compliance checks to the very beginning of the development process.
This shift left approach in DevOps and the overarching shift left methodology embeds automated quality gates into requirements gathering and design sessions, rather than relegating them to post build QA. By shifting left in DevOps, teams adopt a unified left shift strategy, leveraging shift left technology to catch defects and vulnerabilities at their source and drive continuous shift left development.
- A shift left strategy integrates automated unit and integration tests, security analyses (SAST, DAST, IAST), and policy as code enforcement into the initial development stages, requirements, design, and commit.
- By shift left security DevOps and the shift left security approach, teams detect and resolve issues at the point of origin, minimizing rework, reducing context switch overhead, and eliminating late stage schedule slips.
- True DevSecOps shift left extends across the pipeline: unit tests and static analysis in developers’ IDEs; interactive security testing during feature branches; container and dependency scans before packaging; and compliance gates that block unsafe artifacts from promotion.
This shift left methodology answers the question “what is shift left approach?” by aligning Dev, Sec, and Ops around continuous inspection, rapid feedback, and fortified quality, turning every commit into an opportunity for early defect elimination.
What Key Benefits Does a Shift Left DevOps Strategy Deliver?
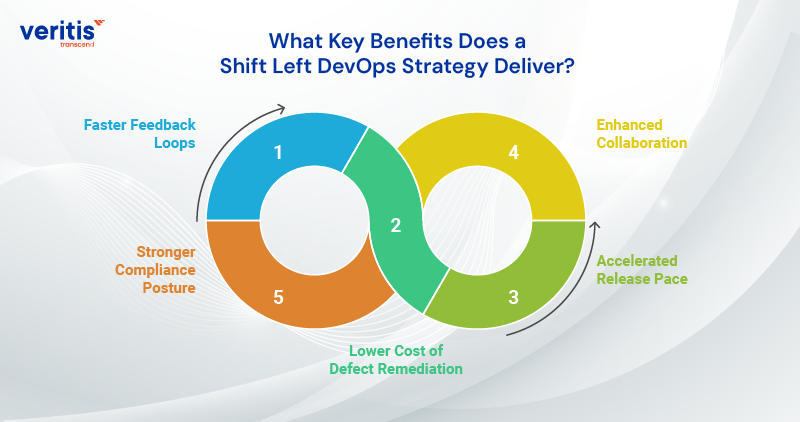
1) Faster Feedback Loops
By integrating automated tests and security scans into every pull request, developers gain real time insights into the code quality and vulnerabilities, slashing average bug fix cycles by up to 50% and keeping projects on schedule.
2) Lower Cost of Defect Remediation
Catching defects during design or code review is 7 to10 times more cost effective than post deployment patches, freeing up budget and resources for innovation rather than firefighting.
3) Accelerated Release Pace
Automated early validation eliminates gatekeeper bottlenecks in test and staging environments, increasing deployment frequency by 30% to 40% and enabling teams to deliver new features with confidence.
4) Enhanced Collaboration
Embedding quality and security ownership across Dev, QA, and Sec teams breaks down silos, builds shared accountability, and accelerates decision making, fostering a culture of continuous improvement.
5) Stronger Compliance Posture
Policy as code and integrated compliance checks ensure regulatory requirements are met at every stage of the pipeline, reducing audit preparation time and minimizing the risk of compliance violations.
Useful link: ITIL vs DevOps: Can Both Concepts Work Together?
Which Best Practices Ensure Successful Shift Left DevOps Adoption?
1) Automated Unit and Integration Testing
- Embed comprehensive test suites in local developer workflows.
- Enforce test coverage thresholds before code merges.
2) Static Application Security Testing (SAST)
- Integrate SAST tools into pre commit hooks and CI jobs to instantly highlight vulnerabilities.
- Shift common misconfigurations and injection risks out of late stage QA.
3) Dependency and Container Scanning
- Scan third party libraries and container images at build time for known CVEs.
- Block insecure dependencies before artifacts enter artifact repositories.
4) Policy as Code and Compliance as Code
- Define infrastructure, network, and access policies declaratively and validate them in the CI/CD pipeline.
- Automate checks against standards (e.g., PCI DSS, GDPR) during pipeline execution.
5) Peer Reviews and Pair Programming
Combine automated checks with human code reviews focused on architecture, logic, and security considerations early in the feature branch lifecycle.
What Phased Roadmap Drives Effective Shift Left DevOps Implementation?
| Phase | Activities | Success Metric |
| Assess | Inventory existing tools, baseline defect rates, and security posture. | Defect and vulnerability baseline |
| Plan | Define “shift left” policy scope; select SAST/DAST tools; train teams. | Policy catalog; toolchain readiness |
| Pilot | Onboard one critical service: integrate tests/scans into its CI pipelines. | % of pipelines shifted left |
| Scale | Roll out to all teams, enforce pass/fail gates, and monitor pipeline metrics. | Deployment frequency, failure rates |
| Optimize | Tweak rules to reduce false positives; automate remediation workflows. | Reduction in manual triage effort |
What Distinguishes Shift Left From Shift Right in DevOps?
| Aspect | Shift Left DevOps | Shift Right DevOps |
| Timing of Validation | Early in development: unit tests, SAST, policy as code during shift left development, and CI builds. | Late/Production: user acceptance, synthetic monitoring, chaos engineering after deployment. |
| Primary Focus | Prevent defects and vulnerabilities through shift left security, DevOps, and automated pre commit gates. | Detect real world issues through logs, metrics, and real user monitoring. |
| Feedback Loop | Fast, in IDE and CI: immediate corrections during DevOps shift left cycles. | Slower, in staging/production: feedback after users interact with the system. |
| Cost Implications | Lower the cost of defect remediation by fixing bugs during code review rather than after release. | Higher operational costs and production remediation demands firefighting and hotfixes. |
| Tooling and Technology | Shift left technology: SAST, unit testing frameworks, policy as code tools. | Production observability: APM, logging platforms, chaos tools. |
| Security Posture | Proactive: Integrate security scans and threat modeling early (shift left security approach). | Reactive: incident response and patching after breach attempts. |
| Security Posture | Proactive: Integrate security scans and threat modeling early (shift left security approach). | Reactive: incident response and patching after breach attempts. |
| Team Collaboration | Requires cross functional collaboration from Day 0, aligning Dev, Sec, and Ops in a shift left methodology model. | Emphasizes collaboration between DevOps and SRE during release and operations. |
| Quality Metrics | Code coverage, vulnerability counts, and build pass rates are the heart of DevOps shift left strategy success metrics. | Uptime, MTTR, customer satisfaction, production error rates, and metrics for shift right effectiveness. |
| Cultural Impact | Empowers developers with ownership of quality and security, reinforcing the DevOps shift left approach mindset. | Cultivates resilience and reliability focus, preparing teams to handle incidents gracefully. |
Useful link: MLOps vs DevOps: Which Drives Greater Business Impact for Your Enterprise?
What Challenges Does Shift Left DevOps Face and How Can They Be Overcome?
1) Toolchain Fragmentation
Teams juggle dozens of point tools, creating integration headaches and inconsistent workflows.
Veritis Solution: We conduct a “Tool Rationalization Sprint” to consolidate your stack around a lean set of interoperable SAST, DAST, IAST, RASP, and CSPM platforms, then deliver a unified dashboard that streamlines enforcement of your shift left strategy.
2) Cultural Resistance
Developers and security teams often view early testing as a blocker rather than an enabler.
Veritis Solution: Through our “Quick Success Pilot Program,” we embed shift left practices in a high visibility project, celebrating early defect catches and publishing ROI metrics to build momentum and secure executive buy in.
3) Alert Fatigue and False Positives
Excessive noise from scans can overwhelm teams and distract them from focusing on critical issues.
Veritis Solution: Our AI driven Triage Engine tunes rules across your SAST/DAST/IAST tools, reducing false positives by up to 70% and focusing your teams on high impact vulnerabilities.
4) Skill Gaps in Secure Development
Not every engineer is a security expert, leading to misconfigurations and blind spots.
Veritis Solution: We launch tailored “Shift Left Academy” workshops and pair each squad with a Security specialist from Veritis, democratizing expertise and embedding best practices in everyday development.
5) Demonstrating Business Value
Without clear metrics, it’s challenging to justify the investment in a shift left methodology.
Veritis Solution: Our “Value Stream Dashboard” captures key KPIs, deployment frequency, defect remediation cost savings, and compliance posture, delivering real time, boardroom ready reports to showcase fast ROI and sustained impact.
Which Testing Tools Underpin a Robust Shift Left DevOps Pipeline?
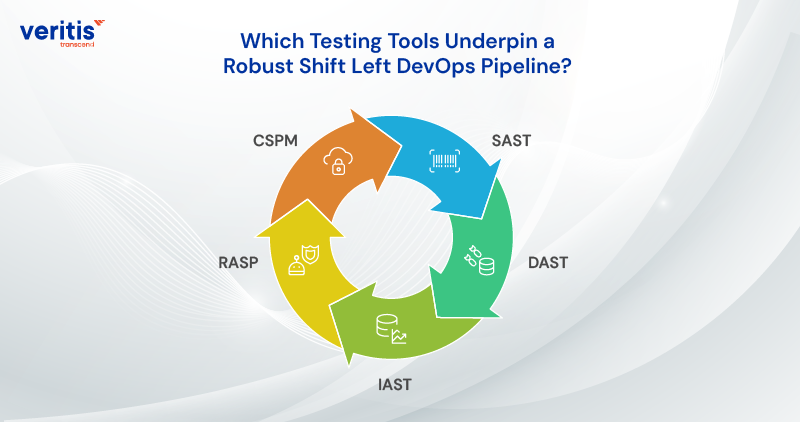
Early stage validation transforms the DevOps shift left by embedding comprehensive testing and security checks into every code commit. Instead of waiting for later phases, teams leverage automated scanners, vulnerability audits, and compliance gates at the point of development to uncover defects before they propagate. This proactive testing model not only enhances code quality and strengthens the security posture but also compresses release cycles, enabling faster and more reliable software delivery.
1) SAST (Static Application Security Testing)
- Integrate SAST into your CI/CD pipeline as part of your shift left approach in DevOps, automating code scans and embodying a proactive shift left methodology to catch vulnerabilities at the source.
- Leverage SAST within a DevSecOps shift left framework to drive shift left development and enforce a robust shift left security approach, ensuring code integrity before runtime.
- Treat SAST as a core shift left technology and shift left strategy. This DevOps shift left practice accelerates secure releases, reduces remediation overhead, and advances your left shift strategy.
2) DAST (Dynamic Application Security Testing)
- DAST simulates real world attacks against your live application, turning each build into a battlefield rehearsal for the shift left DevOps era.
- By executing dynamic probes and interactive scans, you enforce a shift left security approach that uncovers runtime flaws invisible to static analysis.
- Seamlessly woven into CI/CD pipelines, DAST embodies the DevSecOps shift left vision, validating resilience at every release and ensuring your production environment never sleeps.
3) IAST (Interactive Application Security Testing)
- As a core pillar of our shift left methodology, IAST embeds directly into your application’s runtime, streaming real time vulnerability intelligence to your DevOps shift left cockpit.
- By correlating live traffic with code execution, it prioritizes critical flaws with surgical precision, so your teams focus on high impact remediations.
- This strategic tool transforms security from a late stage brake into an early stage accelerator, driving faster releases, reducing enterprise risk, and assuring stakeholders of unwavering reliability.
4) RASP (Runtime Application Self Protection)
- Embed RASP agents within your applications during development to enforce a shift left methodology, transforming runtime defense into an integral part of your shift left development lifecycle.
- RASP auto detects and neutralizes attacks in real time, exemplifying the DevSecOps shift left and shifting left in DevOps by preventing exploitation before code ever reaches production.
- As a critical shift left technology and shift left security approach, RASP turns reactive incident response into proactive protection, aligning with your broader shift left strategy for unparalleled resilience.
5) Cloud Security Posture Management (CSPM)
- Integrate CSPM into your CI/CD pipeline as part of a shift left methodology, proactively surfacing misconfigurations and compliance drift before workloads reach production.
- Leverage CSPM’s continuous cloud monitoring to enforce a shift left security approach, aligning with DevSecOps shift left principles and reducing remediation cycles.
- Adopt CSPM as a core shift left technology within your DevOps shift left and shift left strategy, embedding governance checks that fortify your cloud posture early in the development lifecycle.
Case Study: DevOps Solutions for the Data Analytics Industry
A data analytics firm engaged Veritis to modernize its software delivery pipeline using a shift left DevOps approach. The client struggled with late stage defect detection, slow release cycles, and limited test automation. Veritis introduced early stage testing, CI/CD pipelines, and infrastructure automation to catch issues sooner and accelerate delivery. This proactive, shift left strategy not only improved code quality and reduced time to market but also fostered better collaboration between development and operations, showcasing how early integration of DevOps practices can drive efficiency and resilience in data driven environments and positively impact team dynamics.
Read the complete case study: DevOps Solutions for the Data Analytics Industry.
Conclusion
The shift left DevOps approach transforms delivery pipelines into proactive quality and security engines. By catching issues early, teams accelerate time to market, slash remediation costs, and foster a culture of shared responsibility. Organizations that embed shift left practices position themselves to deliver resilient, compliant software at scale and outpace their competitors in the digital era.
Next Steps:
- Map your current pipeline and identify the first candidate who represents the “left shift.”
- Pilot automated testing and security checks in a single service.
- Measure impact, refine your approach, and expand across the portfolio.
Embrace DevOps shift left with Veritis as your strategic partner. Our experts will tailor and implement the right tools, training, and dashboards to ensure your transformation delivers rapid ROI and sustainable innovation.
Deciding to adopt an approach is not a big deal, but making it succeed is what counts, and this is where Stevie Award winner Veritis comes in. Recognized for its DevOps excellence, Veritis, a leading DevOps consulting company, is the preferred choice of Fortune 500 companies and emerging organizations. We have developed cost effective solutions which don’t hamper quality or reliability. So reach out to us and embrace the best.
Explore DevOps Solutions Got Questions? Schedule A Call
Additional Resources: