
Operational security (OPSEC), also known as procedural security, was created by the US military during the Vietnam War. This application is widely used in business as a risk management plan for preventing sensitive data without malicious intent. So, what is OPSEC? OPSEC is a plan that challenges IT and security professionals to examine their operations and systems from the perspective of a hacker. It includes analytical tasks and procedures, such as social media monitoring, behavioral analysis, and security best practices.
Operational security (OPSEC) is a beacon of innovation and resilience. It ensures that sensitive information remains secure against threats. OPSEC is not just a set of protocols but a dynamic strategy that intertwines advanced technology, human vigilance, and proactive measures to safeguard data. It encapsulates the essence of foresight and precision, transforming how organizations protect their most valuable assets.
Picture a state of the art control center where every access point is continuously monitored, every movement meticulously analyzed, and any irregularities promptly addressed. This is the role of OPSEC in the digital realm. By detecting potential threats and vulnerabilities before they can be exploited, OPSEC defends against breaches and fosters a culture of security and trust within organizations. It’s about developing an environment where employees are empowered and informed, technology works seamlessly to predict and prevent, and clients feel confident that their information is safe.
OPSEC aims to close all security holes that allow threat actors to steal sensitive data from an organization. Robust security isn’t about having the proper hardware or software; it’s about knowing exactly how they work and where the gaps are. When used alone, not every type of information is regarded as sensitive. However, if a hacker combined this data, they could use it for different things, such as creating convincing phishing emails or accessing user accounts.
Raising awareness of this problem can be challenging. The OPSEC approach produces a framework for adopting policies and best practices. Whether an organization can set guidelines for employees depends on the vulnerabilities and threats to its business that have been detected. This blog post will explain OPSEC’s five steps and best practices.
Talk To Our Operational Security Expert
What is Operational Security?

OPSEC is a military term for plans to prevent potential enemies from learning important information about operations. This concept has transferred from the military to other branches of the federal government, including the Department of Defense (DOD). OPSEC plans are now used in corporate operations as information management and protection, which have become crucial to success in the private sector.
OPSEC is all about securing sensitive information in an organization. It employs specific governance techniques to manage security operations risk continuously. Your enterprise uses OPSEC daily, even if you aren’t aware of it. The OPSEC consulting process can be as easy as placing a firewall between your system and the Internet to aid in the securement of information and ensure the proper disposal of hard copies.
Before you can deploy OPSEC security, you must determine the location and type of your storage. OPSEC keeps information in two categories: tacit and explicit. Both are significant liabilities in terms of a company’s productivity. The OPSEC process helps businesses address corporate data, information security operations, data security services, and risk management. It is employed by companies keen to safeguard their valuable data.
Importance of Operational Security
Recognizing the importance of Operational Security (OPSEC) is crucial for organizations safeguarding their financial well being. By implementing rigorous OPSEC consulting measures, organizations can prevent significant monetary losses from security operations services breaches. Strong OPSEC offers several key benefits:
- Safeguarding Against Intellectual Property Theft: Prevents competitors from gaining access to proprietary processes or technologies, preserving the original innovators’ market advantage and revenue generation.
- Mitigating Legal Expenses: It reduces the risk of lawsuits from data breaches that compromise customers’ personal information and limits potential fines for non compliance with industry regulations such as GDPR or HIPAA.
- Prevention of Ransomware related Costs: This product protects against malware and ransomware attacks that could encrypt critical systems and demand substantial ransoms for decryption keys.
- Minimizing Costs Associated With Business Disruption: Reduces downtime resulting from cyber attacks, which directly translates to diminished productivity and sales.
Useful link: Securing Digital Transactions: Addressing Unique Cybersecurity Challenges in Banking IT
The 5 Key Steps of Operational Security
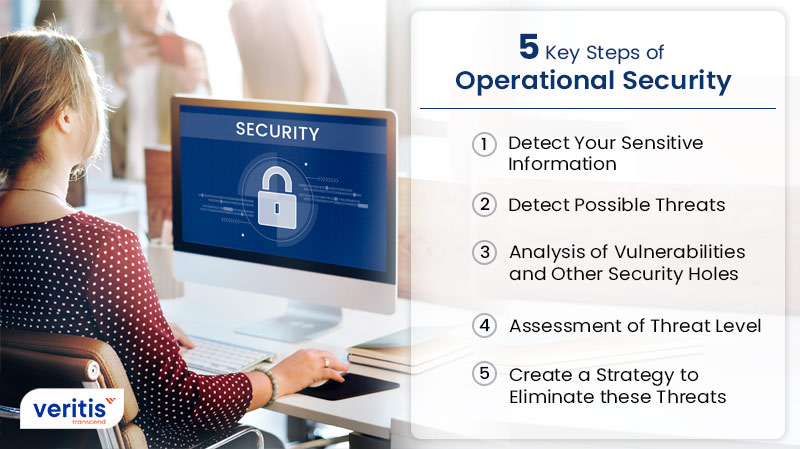
The five steps combined in the OPSEC process allow companies to secure their data processes.
1) Detect Your Sensitive Information
The first essential step in ensuring OPSEC security is understanding businesses’ data and the sensitive information they maintain on their systems. This includes detecting user information such as client data, financial information, employee details, and intellectual property. Companies must concentrate their resources on protecting this essential data.
2) Detect Possible Threats
The next stage is to identify the potential threat matrix to your business. Companies must assess the potential threats once the sensitive data has been recognized. Identifying who can pose a severe threat allows you to evaluate the risk depending on the skill set of the possible opponent.
3) Analysis of Vulnerabilities and Other Security Holes
This is a key step in the information risk management process. The business must scour any security gaps that might allow threats to be displayed. Assess the current condition of your security operations services to detect flaws that could be exploited to access your sensitive data. This should combine software and hardware data security solutions, including automated security patch updates, employee awareness and training, and best practices like 2FA and strong passwords.
4) Assessment of Threat Level
The next step is to determine the threat level associated with the most discovered vulnerabilities. Next, the organization ranks the risks based on various factors, including the likelihood that a given assault would occur and the potential impact such an attack would have on operations. The system’s threat level is determined to be low, medium, or high.
5) Create a Strategy to Eliminate these Threats
This data enables companies to create a comprehensive strategy to address the identified threats. The last step in OPSEC security is implementing countermeasures to eliminate threats and reduce cyber security operations risks. These frequently involve developing policies for protecting sensitive data, upgrading hardware, and training staff members on security best practices and corporate data regulations.
Useful link: Securing the Future: AI Automation Tools in Cybersecurity
Making the OPSEC Process Adaptive and Real Time in 2025
While the five step OPSEC process, which involves identifying critical information, analyzing threats, assessing vulnerabilities, applying countermeasures, and evaluating the effectiveness of these measures, remains the foundation, today’s threat landscape demands a shift from a static checklist to a dynamic, adaptive control framework. In 2025, operational security must continually respond to real time threats, including insider breaches, behavioral profiling, and AI driven social engineering.
Modern OPSEC strategies now incorporate AI powered risk scoring, continuous monitoring of user behavior, and identity based access controls. These enhancements enable proactive detection and faster containment of threats well before they escalate. For example, organizations using adaptive insider risk models have reported a 59% reduction in false positives, a reassuring sign of the effectiveness of these strategies, boosting operational resilience and decision making clarity.
To stay ahead, enterprises should embed operational security controls, such as multifactor authentication, least privilege access, and behavioral analytics, directly into every step of the OPSEC lifecycle. This is not just a recommendation, but an urgent action that can significantly enhance an organization’s security posture.
Common Operational Security Threats
Operational Security (OPSEC) is essential for protecting critical data from various threats. Understanding these threats and the tools available to combat them is crucial for maintaining a secure environment.
1) Phishing Attacks
Phishing attacks use fake messages that mimic trusted sources. These attacks typically aim to steal sensitive data like login credentials and financial information. Attackers use email, social media, phone calls, and fake websites to deceive users into divulging confidential information.
2) Malware
Malware includes various malicious software types such as viruses, worms, Trojans, ransomware, and spyware. These harmful programs can infiltrate systems, steal or damage data, and disrupt operations. Adequate malware protection is crucial for maintaining operational security.
3) Insider Threats
Insider threats come from employees or associates within the organization who misuse their access to data and systems. These threats can be intentional, like data theft for personal gain or accidental data leaks. Regular monitoring and strict access controls help mitigate these risks.
4) DDoS Attacks
Distributed Denial of Service (DDoS) attacks point to overwhelm a network, service, or website with excessive traffic, rendering it unusable. These attacks can cause significant operational disruptions and financial losses. Implementing robust network defenses can help prevent and mitigate DDoS attacks.
5) Social Engineering
Social engineering attacks exploit human psychology to gain unauthorized access to systems or information. Attackers manipulate individuals into breaking standard security procedures, often through impersonation, persuasion, or intimidation. Educating employees about these tactics is essential for defense.
Emerging Threats and Real World OPSEC Breakdowns in 2025
As OPSEC evolves, so do the threat vectors. The urgent rise of human centric attacks, leveraging social engineering, behavioral profiling, and even digital fingerprinting, necessitates the immediate adaptation of security strategies that go beyond traditional policies and firewalls.
A recent incident in March 2025 highlighted this risk when senior government officials inadvertently leaked sensitive operational details through unsecured Signal chats. This real world example underscores how lapses in need to know discipline and failures in data security in the cloud and collaboration platforms can rapidly compromise critical operations, with severe downstream consequences.
Modern attackers now exploit not just digital vulnerabilities, but also cross channel fingerprinting and stylometry, where writing patterns and behavioral traces can reveal identity or intent even when users think they’re anonymous.
Organizations must now treat OPSEC as a continuous behavioral shield, not just a checklist. This includes the crucial need for ongoing training to recognize these subtle threats and the constant enforcement of secure habits across all communication channels, emphasizing the importance of ongoing vigilance.
Useful link: How SaaS Business Intelligence is Revolutionizing Data Driven Decision Making
What Are the Key OpSEC Tools and Technologies?

Various OPSEC tools and technologies are employed in OPSEC strategies to effectively combat these threats.
1) Intrusion Detection Systems (IDS)
Intrusion Detection Systems continuously scan network traffic to identify unusual behavior and potential threats, providing alerts when potential intrusions are detected. IDS can help identify and respond to threats before they cause significant damage.
2) Security Information and Event Management (SIEM) Systems
SIEM systems gather and evaluate data from diverse security devices and systems within an organization. They offer real time analysis of security alerts generated by both hardware and software, assisting in detecting and responding to potential threats more efficiently.
3) Security Incident and Event Management Systems
Like SIEM, Security Incident and Event Management systems focus on identifying, managing, and mitigating security incidents. These systems provide comprehensive incident response capabilities, ensuring swift action to minimize damage.
4) Antivirus Software
Antivirus software safeguards against various types of malicious software. It scans for and eliminates viruses, worms, Trojans, and other forms of malware. Frequent updates defend against new and emerging threats, ensuring systems remain secure and functional.
5) Encryption Tools
Encryption tools secure data by transforming it into an unreadable format, accessible only to those with the appropriate decryption key. This technology is essential for safeguarding sensitive information both during transmission and while stored, preserving data privacy and integrity.
Best Practices for OPSEC
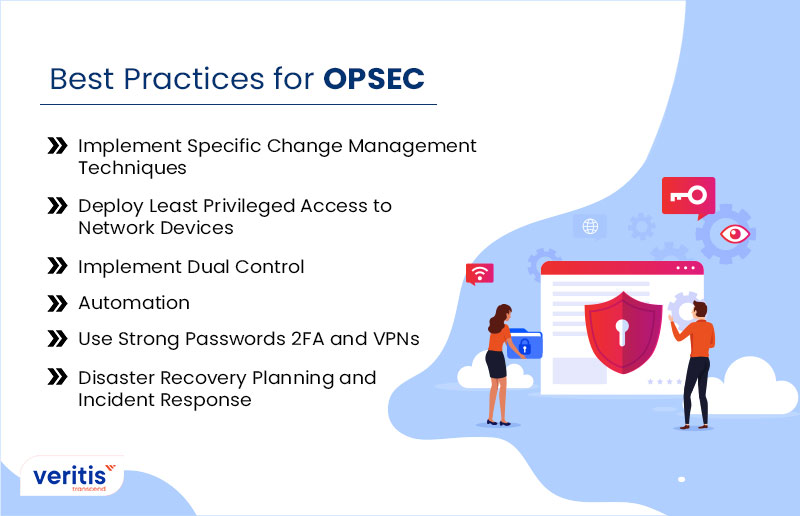
OPSEC consulting process steps apply risk management plans to detect potential threats and vulnerabilities before they are abused and pose business issues. By following the six best practices, a company can build and implement an effective and robust security plan.
1) Implement Specific Change Management Techniques
Companies must put the right change management plans in place for staff members to follow in case network modifications are performed. All modifications must be controlled and managed so companies can audit and monitor the alterations.
2) Deploy Least Privileged Access to Network Devices
Allow the least access to network devices using authentication, authorization, and accounting (AAA). Employees must have the minimum access to resources, networks, and data to operate successfully. This involves applying the least privilege principle, which ensures that every program, process, and user has the minimal privileges necessary to carry out their tasks.
3) Implement Dual Control
Organizations must verify that the teams and individuals who manage IT security operations differ from those who work on your network. This strategy protects against issues like conflicts of interest and others.
4) Automation
Regarding business security, people are often the weakest links for data. In addition, human errors can result in details, mistakes, critical processes, and forgetting things. Automation can reduce these errors.
5) Use Strong Passwords, 2FA and VPNs
Data breaches frequently result from human error. It would help if you verified that strong passwords and two factor authentication (2FA) are used on every user account and trained employees on potential phishing threats. VPNs should be used while transferring data or working remotely to ensure the data is securely encrypted.
6) Disaster Recovery Planning and Incident Response
Solid disaster and incident response plans are key components of any security defense. Even with operational technology security measures, you still need a plan for identifying risks, dealing with them, and mitigating the potential risks.
Useful link: Cloud Security Automation: Best Practices, Strategy, and Benefits
Benefits of Operational Security (OPSEC)

1) Protection of Sensitive Information
- OPSEC process steps help safeguard sensitive information from adversaries, preventing unauthorized access or exploitation.
- By identifying critical information, OPSEC security ensures that only approved personnel can access it, reducing the risk of leaks or breaches.
2) Improved Risk Management
- OPSEC enables organizations to identify and prioritize potential risks to their operations.
- OPSEC minimizes these risks by implementing appropriate countermeasures and enhancing overall operational resilience.
3) Preserved Reputation and Trust
- Adequate OPSEC security maintains the reputation and trust of organizations by preventing damaging disclosures.
- It ensures that sensitive information, such as proprietary data or customer details, remains secure, preserving public trust.
4) Legal and Regulatory Compliance
- OPSEC helps organizations comply with legal and regulatory requirements to protect sensitive information.
- By safeguarding classified or sensitive data, OPSEC ensures adherence to laws and regulations governing data privacy and security.
5) Competitive Advantage
- OPSEC process steps provide a competitive advantage by safeguarding proprietary information and trade secrets.
- It prevents competitors or adversaries from accessing valuable intellectual property or strategic plans.
Useful link: Fortifying Your CI/CD Environment: Best Practices for Defending Against Security Threats
6) Adaptability and Flexibility
- OPSEC practices can adapt to threats and operational technology cyber security environments, ensuring effectiveness.
- Organizations can adjust their OPSEC measures to address emerging risks and challenges by remaining flexible.
7) Reduced Vulnerability to Espionage
- OPSEC mitigates the risk of espionage by limiting the amount of sensitive information available to potential adversaries.
- It prevents hostile actors, including foreign intelligence agencies, from gathering intelligence that could compromise national security or corporate interests.
8) Cost Savings
- OPSEC helps avoid the financial consequences of security breaches, including legal fees, regulatory fines, and reputational damage.
- By investing in proactive security measures, organizations can reduce the potential costs related to data breaches or operational technology cybersecurity
Rules to Use for OPSEC
Let’s explore some rules to use to secure your data online.
- Don’t share your personal information, such as IP addresses, emails, and cookies.
- Don’t risk it by visiting online areas, such as the dark web.
- Sending encrypted data isn’t recommended
- Don’t reveal any personal information about yourself
- Don’t believe untrustworthy websites
Enterprise Grade OPSEC Controls and Governance
Operational security isn’t just about protecting information; it’s about embedding governance into every operational decision. Enterprises today must deploy a layered, control driven strategy that enables both agility and accountability.
Key governance grade OPSEC controls include:
- Least Privilege Access: Limit access strictly to those who need it to perform their duties.
- Zero Trust Enforcement: Authenticate every request, verify each identity, and never trust by default.
- Dual Control Approvals: Implement two person rule or executive oversight for mission critical decisions.
- Automated Logging & Change Audits: Monitor every operational change with full traceability and alerts.
- Multifactor Authentication (MFA): Mandate MFA for all systems, tools, and remote access points.
- Separation of Duties & Trustee Rotation: Reduce insider threat exposure through mandatory role rotation.
These controls not only harden your OPSEC posture but also align it with enterprise risk management and compliance mandates, providing you with a strong foundation for security and regulatory compliance.
Most importantly, OPSEC should be a living culture led by leadership, reinforced through behavior, and measured via security maturity models. Your active participation in this measurement process is crucial, and your accountability is key to its success.
Case Study: Strengthening Operational Security Through IT and Database Modernization
Veritis collaborated with a prominent HR solutions provider to modernize their database systems and IT infrastructure, aiming to enhance the security, integrity, and availability of sensitive data. The client faced risks stemming from outdated systems, limited access controls, and scattered data repositories, all of which posed potential operational security (OpSec) vulnerabilities. Veritis implemented a robust, centralized database architecture, enhanced system governance, and strengthened security protocols to safeguard critical HR and employee data. This real world example illustrates how operational security is closely tied to infrastructure modernization and data handling practices, particularly in industries that manage high volumes of confidential information.
Read the Complete case study: Strengthening Operational Security Through IT and Database Modernization.
Final Thoughts on OPSEC
Risk management combines detecting flaws and threats before the issue arises. OPSEC compels managers to scrutinize their operations to detect any points where their information is vulnerable. IT Managers can detect flaws they might have overlooked by viewing processes from the view of a malicious third party. Then, they can implement the appropriate countermeasures to secure sensitive data.
Veritis, the Stevie Awards and Globee Business Award winner, offers a wide range of solutions that guide businesses to enhance their most sensitive data, improve their data security, and ensure the constant security of their users and devices. We have enough expertise in providing cybersecurity solutions in a dynamic environment. So, contact us and work without further ado to protect your proprietary data before it’s too late.