
Table of contents
With the introduction of the cloud, there is no aspect of your IT infrastructure that other people or businesses cannot handle for you. Many companies rely on Amazon AWS to provide the computing and storage resources required to run their websites and applications. Others purchase a complete platform from a third-party vendor that includes servers, databases, middleware, operating systems, and other components. They use hypervisors and other tools to access high-level APIs from online services.
Others, however, rely on software and application providers from outside sources. Now, rather than investing in developing their infrastructure or building, maintaining, and creating these resources, companies can more easily, quickly, and affordably meet their IT requirements. In addition, over time, it has become possible to access almost everything as a service, including storage, logging, disaster recovery, and backends. Even services like security are now possible.
Security as a Service, or SECaaS, is what you offer when outsourcing your security to a cloud business. In today’s environment, companies can leverage Managed IT Security Services to ensure their infrastructure is secure without the need for in-house security resources. Of course, you must continue to pay the vendor for their services after they have been integrated into your infrastructure. However, you will receive the assistance you require. You won’t need to invest in personal, software, or other resources.
What is Security as a Service (SECaaS)?
Security as a Service (SECaaS) enables companies to outsource their cyber security management as a service requirement. Outsourced data security solutions include anti-virus protection, intrusion detection, and data loss prevention. In addition, businesses can benefit from the expertise and innovation of a committed cyber security service team specializing in breach prevention in security as a service in a cloud computing environment by working with an SECaaS vendor.
Security as a Service provider eliminates the need for local delivery of data security solutions. Your IT department installs anti-virus, spam filtering, and other data security solutions on each computer, keeping the program up-to-date or instructing them to use it on the network security protection or server in your place of business.
The traditional method is also expensive. You must pay upfront expenditures for the hardware and ongoing license fees to use the program. However, thanks to security as a service, using the same technologies with just a web browser is now easy and affordable.
In the same way that software as a service (SaaS) companies do, security as a service provider frequently charges a monthly subscription fee to pay for the expenses of outsourcing services. However, they offer security for your cloud-based apps, data, and operations rather than granting you access to a tool or platform.
Transforming Cloud Security With Security as a Service (SECaaS)
Organizations encounter significant challenges in protecting their digital assets. This is where Security as a Service in cloud computing steps in—a revolutionary approach transforming how businesses protect their data, applications, and networks.
Envision your cybersecurity needs with precision and expertise, all without the overhead of on-premises infrastructure. With SECaaS, information security as a service team collaborates seamlessly with specialized providers to deploy state-of-the-art security tools directly from the cloud. This streamlines your defenses while providing a cost-effective, scalable solution that adapts to the threat domain.
Gone are the days when organizations relied solely on a single security provider. Today’s complex cybersecurity environment demands a multi-layered strategy. SECaaS allows you to draw from a diverse pool of specialized security experts, each bringing unique skills to tackle specific challenges. Whether safeguarding against malware, conducting vulnerability assessments, or managing identity and access, SECaaS provides a holistic, tailored defense strategy that evolves with your needs.
Useful link: Things CTO Needs to Consider Selecting a Cloud Network Security Solution
Transformative Examples of Security as a Service (SECaaS)

1) Network Security
Manage access, monitor activity, and protect your network from unauthorized users with comprehensive network security tools, ensuring only legitimate traffic flows through.
2) Web Security
Protect your online presence with web security tools that prevent attackers from exploiting your applications or compromising your network.
3) Continuous Monitoring
In a world where threats never sleep, continuous monitoring ensures your cloud security as a service is constantly under surveillance, promptly detecting and mitigating potential threats.
4) Business Continuity
Business continuity tools ensure that your critical systems remain operational despite disaster, providing uninterrupted service and maintaining customer trust.
5) Identity and Access Management (IAM)
With IAM, you can precisely control who accesses your network and applications. You can also know who can access what, safeguarding sensitive information from unauthorized users.
6) Encryption
Encryption ensures that even if threat actors intercept your data, it remains indecipherable, turning potential threats into mere background noise.
7) Disaster Recovery
SECaaS tools enable swift recovery when unexpected strikes occur, ensuring your operations bounce back quickly and minimizing downtime and disruption.
8) Security Information and Event Management (SIEM)
Gather and assess security event data across your organization, providing critical insights into potential security breaches or system vulnerabilities.
9) Data Loss Prevention (DLP)
Imagine having a vigilant guard over your most valuable asset—your data. DLP tools ensure your data is secure, monitored, and protected from breaches, whether at rest or in motion.
10) Email Security
Protect your business from sophisticated email-based threats like phishing and malware. SECaaS tools shield your communication channels, keeping them secure and trustworthy.
11) Security Assessment
Regular security assessments ensure your defenses are robust and up to date, aligning with industry standards to tackle emerging threats.
12) Intrusion Management
Proactively identify and neutralize potential intruders before they can compromise your systems, maintaining the integrity of your digital environment.
13) Vulnerability Scanning
Stay ahead of cybercriminals by regularly scanning your IT infrastructure for vulnerabilities and identifying and addressing weaknesses before they can be exploited.
SECaaS represents a paradigm shift in how businesses approach cybersecurity—offering a dynamic, scalable, cost-effective solution to protect digital assets. By leveraging the power of the cloud and specialized expertise, SECaaS fortifies your defenses and empowers your organization to innovate confidently. Embrace the future of cybersecurity with SECaaS and ensure your digital journey is secure, resilient, and forward-thinking.
Useful link: Top 10 Security Issues in Cloud Computing
Security as a Service Benefits
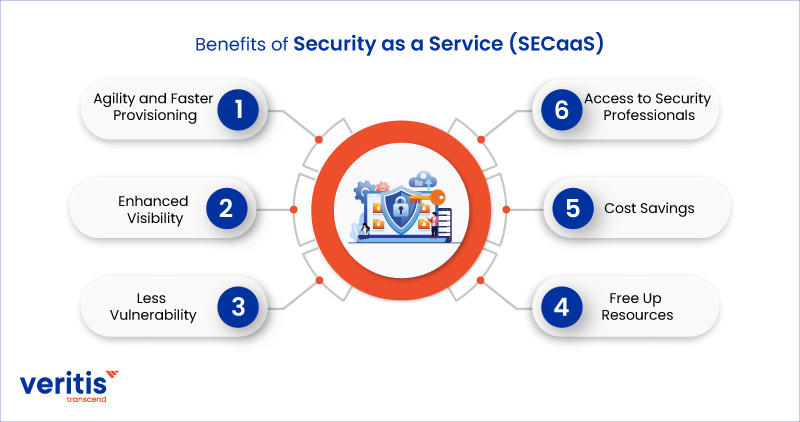
1) Agility and Faster Provisioning
One of the best aspects of as-a-service solutions is the ability to grant your users access to these tools immediately. In addition, SECaaS solutions are available on demand where and when you need them and may be scaled up or down as needed. That means there is no longer any ambiguity regarding deployment or upgrades because your SECaaS supplier will handle both for you and make it all apparent through a web-based dashboard.
2) Enhanced Visibility
Thanks to cloud security as a service, your business can see all its traffic, application security as a service being used, and any hacked IoT devices, threats, and policy violations being stopped—and much more—in real-time. An integrated cloud solution offers a centralized view of all activities across cyber security services, including firewall, sandbox, secure web gateway, advanced threat protection, data loss prevention, bandwidth control, and more. This resembles information security as a service and event management (SIEM) system.
3) Less Vulnerability
Attackers increasingly focus on mobile users and exploit mobile devices as a beachhead to assault business systems. Since bad actors today are aware that legacy security in the data center cannot protect these users.
Your network security protection is at risk if you can’t secure every link. Cloud security fills enterprise security holes created by off-net users and people connecting directly to cloud apps and the public internet.
4) Free Up Resources
When security provisions are managed externally, your IT teams may concentrate on what is critical to your company. SECaaS frees up resources and provides complete visibility through management dashboards. A group of outsourced security experts skillfully manages your cloud security as a service, assuring you of its effective management.
You can also decide to delegate security procedure management to your IT staff. This will empower your IT teams to control security processes and manage all policy and system changes through a web interface.
5) Cost Savings
One of the main advantages of a security as a service approach is the ability of a firm to save money. A cloud-delivered service is frequently offered in subscription tiers with various upgrade possibilities. It allows a firm to pay for what it requires at the time. Additionally, expertise is optional.
6) Access to Security Professionals
When you utilize SECaaS, you get seasoned, qualified security experts instead of your in-house team, which may need more specialized knowledge or be overburdened with other tasks and unable to devote the necessary attention to cybersecurity.
Useful link: Data Security in the Cloud Solutions Every Modern Business Needs
Challenges of Security as a Service (SECaaS)
Cloud security challenges exist for all security solutions. With an outsourced security solution, there are several issues to consider, such as the following:
1) Eliminating Legacy Hardware Through a Migration
It is impossible to overestimate the advantages of cloud security as a service. Still, your company may be susceptible during the transitional period between dumping legacy security and using the cloud.
2) Misconfiguration Risk
This relates to accountability, but it’s important to note that configuration errors are the leading source of cloud data breaches. In addition, there may be issues if your team or a managed security service provider makes a provisioning error.
3) Accountability
According to a shared responsibility model, the managed security service provider and the client share some blame for a cloud IT services incident. However, no matter who is at fault, the consequences are the same if security problems occur during cloud security as a service deployment. Companies can mitigate the risks associated with outsourced security solutions by implementing and enforcing rules that address vulnerabilities in cloud security.
Gartner predicts that until 2025, customers would be held liable for 99% of cloud security failures rather than cybersecurity service providers.
Useful link: 5 Key Benefits of Implementing Cloud Financial Services for Your Business
How to Select the Best Security as a Service (SECaaS) Provider

1) Service Availability
Ensure the SECaaS provider you select delivers the best uptime for cloud applications, security dashboards, and network security protection resources. A technically competent customer service team should also be available to assist you immediately with unforeseen problems.
2) Partners as Vendors
Research the vendor partners of the security service you are considering. As a service provider supplier, ensure security by utilizing cutting-edge technology and customary cloud services.
3) Service Level Agreement (SLA) and Response Time
Discuss the vendor’s response time when you receive a demo of their services. Before signing the agreement, you can also include a condition in the contract specifying a specific SLA and response time.
4) Disaster Recovery Planning
A disaster recovery plan is crucial to business continuity and can help you avoid losing thousands of dollars during a disruption. Therefore, your SECaaS solution must offer disaster recovery alternatives that can specifically adapt to your company’s requirements.
5) Vendor Lock-in
Avoid signing up for subscriptions with vendor lock-in. Instead, always select subscriptions with flexible terms and simple cancellation procedures.
6) Reporting
Your managed security service provider should grant you access to a simple security tool where you can keep track of the overall security strategy.
Useful link: The Impact of Cloud Integration on Managed Data Services
Features of Security as a Service (SECaaS)

Service-based security on-premises solutions need more special capabilities than technology offers.
1) Possibility of Automation
Cloud security architects can design logic and schema to automate specific operations because the cloud isn’t constrained by hardware and can be continuously improved. As a result, they make life easier for administrators, threat hunters, SecOps teams, and others.
2) Enhanced IoT/OT Security
Legacy security cannot scale to meet modern data protection standards when securing data that enters and leaves IoT and OT-connected machines, devices, and other objects. As your organization generates more data, SECaaS scales to secure it.
3) Zero Track Capability
Cloud-delivered architecture is the only way to achieve zero trust security. No matter what devices users sign in from, security policy is always followed by zero trust. This cannot be done using legacy architectures.
Case Study: Strengthening Financial Security Through Managed IT and SECaaS
Veritis collaborated with a major financial services provider to address critical infrastructure vulnerabilities and streamline server maintenance operations. The client faced increasing risks due to outdated systems, inconsistent patching, and evolving cyber threats. Veritis stepped in with a tailored solution that combines IT infrastructure modernization and Security as a Service (SECaaS) principle, automating updates, enhancing network monitoring, and implementing centralized security controls. The result was a 30% reduction in downtime, a 40% improvement in compliance, and a fortified security posture.
This real-world implementation highlights the proactive nature of SECaaS in today’s threat landscape, offering businesses proactive protection, flexibility, and peace of mind.
Read the complete case study: IT Infra Security and Server Maintenance: Key to Financial Services.
Final Thoughts
Enterprises and SMBs are increasingly choosing security as a service provider solution. However, the growing use of SECaaS is fuelled by the lack of security resources, such as qualified professionals, tools, and skills, as well as the constantly evolving threat landscape. The increasing variety of mssp services also influences the adoption of SECaaS as businesses seek out the best types of cloud services to meet their needs.
Today, outsourcing the management, application, and control of the intricate security field makes sense for many businesses, and it’s proving to be a financially wise investment for those who take advantage of it. Veritis, the American Business Awards, and Globee Business Awards winner, offers cloud-delivered endpoint security and workload protection for your SECaaS requirements. Ready to transform your cybersecurity strategy? Contact Veritis today to explore how SECaaS can protect your business in the digital age.
Schedule A Call with SECaaS Consult
Also Read: