
With rapid advancements in enterprise IT, organizations are under pressure to balance operational agility with airtight cybersecurity. While innovations in cloud computing, remote work, and SaaS apps improve productivity, they also introduce new security vulnerabilities. Traditional access control systems no longer suffice.
This is where Identity and Access Management (IAM) tools become critical. They ensure secure access governance, identity lifecycle management, and policy based user provisioning across dynamic IT environments.
Continuous technological evolution is posing severe challenges for organizations worldwide. While intelligent solutions offer benefits, technological advancements also indirectly create room for cybersecurity threats.
These threats are fast emerging and growing. Therefore, you cannot rely on traditional solutions to manage and safeguard your organizational data and assets from these risks.
Moreover, the rate of cyberattacks is rising year over year, causing organizations to incur trillions of dollars in financial losses. You would require Identity and Access Management services and solutions here.
In this article, we explore the top IAM tools by use case, the business value they deliver, and the core security protocols that drive successful IAM implementation.
Different Identity and Access Management (IAM) Tools By Use Cases
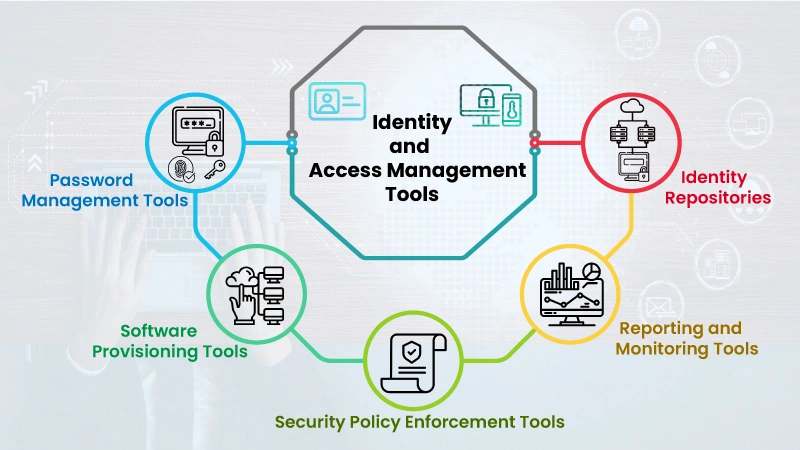
There is a wide range of IAM tools for different business use cases:
1) Password Management Tools – These tools help manage all passwords easily without memorizing them every time.
2) Software Provisioning Tools – These tools help manage user information across systems and applications.
3) Security Policy Enforcement Tools – These tools ensure timely detection of improper behavior, trace real time access, and effectively enforce business policies.
4) Reporting and Monitoring Tools – These tools monitor accounts vulnerable to risks and apps with granted permissions.
5) Identity Repositories – All the information about users and groups is stored.
How IAM Tools Benefit Your Organization
IAM solutions offer more than just secure logins. They drive operational excellence, regulatory compliance, and business resilience.
1) Strengthened Security Posture
IAM tools provide peace of mind by protecting against credential based attacks, enforcing multi factor authentication (MFA), and reducing the attack surface with least privilege access.
2) Business Process Automation
They automate identity provisioning, entitlement management, and access certification, relieving you of manual tasks and reducing the risk of human error.
3) Improved Workforce Productivity
By centralizing identity services and enabling Single Sign On (SSO), IAM tools play a crucial role in minimizing access friction and increasing employee efficiency, thereby improving workforce productivity.
4) Secure Third Party Collaboration
IAM supports external identity federation, allowing secure collaboration with contractors, vendors, and partners without compromising your security perimeter.
5) Centralized Visibility and Governance
Using unified access control policies, IAM platforms offer granular control, reporting, and audit trails that help meet compliance standards like GDPR, HIPAA, and ISO 27001.
How Identity Access Management (IAM) Tools Help Your Business?

IAM Tools support your business majorly in the following areas:
1) Enhanced Security
Compromised user credentials are the first entry points for any intruder attack. IAM Tools ensures your credentials and networks are secured under different security layers.
2) Business Productivity
Managing and controlling access in a large enterprise is tedious and eventually affects productivity. IAM tools help with access management and control, saving related costs.
3) Employee Productivity
A full IAM system alleviates the maintenance burden on your IT teams. IAM tools help your teams efficiently manage identities and access across various networks distributed across locations. Thus, employee productivity is a significant advantage. Centralized control in the IAM system naturally reduces the number of reports to core security teams.
4) Improved Collaboration
IAM tools contribute to the collaboration among internal and external teams. These include employees, partners, suppliers, and contractors, among others, who can be assisted through modern applications in a more secure manner.
5) Centralized Control
IAM tools facilitate centralized control for storage, access, and control of your data and assets. This reduces the threat from internal and external factors. Options like Single Sign On allow single time authentication for access across multiple platforms.
Beyond Tools, Security Protocols Matter!
While tools can help you get the desired output, the effective implementation of IAM requires adhering to three major Security Protocols:
- A multi factor Authentication System involves multiple authentication methods from different credential categories to verify user identity or authenticate a transaction.
- Identity Management Assessment is crucial for protecting critical identities through an access control mechanism and monitoring who gains access to organizational data.
- Implementation and Integration demand advanced integrations, such as machine intelligence, AI, biometrics, and risk based assessment, across all platforms and devices to remain safe from external and internal threats.
Case Study: Services Firm Migrates from SailPoint to Azure AD
Veritis guided a large professional services firm grappling with costly on premises SailPoint licensing, fragmented user workflows, and manual provisioning through a seamless migration to Azure Active Directory. We conducted a phased cutover, synchronizing users and groups, automating access workflows with Azure Automation and PowerShell, and implementing Azure AD Conditional Access and MFA while maintaining uninterrupted operations. As a result, the client slashed licensing and infrastructure costs by over 50%, reduced IAM support efforts by 30%, bolstered security with native conditional access controls, and achieved full audit ready compliance within a remarkably short timeframe of weeks.
Read the complete case study: Successful Migration of a Services Firm from SailPoint to Azure AD.
Conclusion: Choose IAM That Scales with You
In a hyperconnected digital landscape, Identity and Access Management tools are no longer optional; they’re foundational. Whether you’re a growing business or a global enterprise, the right IAM strategy helps secure your users, data, and infrastructure.
When implemented with robust security protocols and compliance frameworks, IAM can streamline operations, lower IT overhead, and protect against both internal and external threats.
Effective IAM implementation of all these processes requires subject matter expertise and a deep understanding of real time scenarios.
Need expert guidance in IAM implementation or cloud identity migration?
Get in touch with Veritis IAM consultants to accelerate your secure digital transformation.