
Table of contents
- What is Identity and Access Management (IAM)?
- What Does IAM Mean?
- Why do You Need IAM?
- How Does IAM Work?
- What Does IAM Do?
- Does IAM Improve Regulatory Compliance?
- What are the Benefits of IAM?
- How Do IAM Technologies and Tools work?
- IAM Tools
- What are the Challenges and Risks of Implementing IAM?
- What is the Difference Between Identity Management and Access Management?
- How to Deploy Your IAM System: Cloud vs. On premises
- What is AWS Identity and Access Management?
- What Does an IAM Implementation Strategy Include?
- Conclusion
What is Identity and Access Management (IAM)?
Identity and access management (IAM) is the security practice that enables authorized entities (people or things) to access the appropriate resources (applications or data) at the appropriate times. For instance, customers and employees are IAM system users. IAM solutions allow IT managers to verify that users are who they claim to be and that users are only accessing resources and apps they are authorized to use.
Enterprise identity management solutions and access systems help your company manage employee apps without requiring an administrator to log in to every app. In digital transformation services, identities are also assigned to robots, IoT devices, and software components such as APIs and microservices. In addition, Software as a service (SaaS) solutions and multi cloud hybrid IT infrastructures make the IAM framework landscape even more challenging.
An Identity and access management system is essential for any organization because it provides barriers between users and critical enterprise assets. In addition, it helps defend against compromised user credentials and easily cracked passwords, which are common entry points for malicious actors seeking to install ransomware or steal data.
IAM solutions ensure corporate productivity and the smooth operation of digital systems. Employees may conduct business as usual no matter where they are, and centralized management ensures they have access to the resources for their tasks. Additionally, granting access to consumers, vendors, and suppliers can boost productivity and reduce costs.
What does IAM Mean?

IAM ensures that the appropriate individuals and job functions within your business can access the resources required to perform their duties. With the help of IAM solutions, your company can manage staff apps without having to log in as an administrator to every app. An identity access management system allows your enterprise to manage different identities, including users, software, and hardware devices.
Useful link: Key Business Benefits of Identity and Access Management
Why do You Need IAM?

Organizations require IAM architecture to embrace employee productivity and offer online security.
1) Productivity
Once online at your leading IAM portal, your employees don’t need to worry about having the proper password or access level to perform their jobs. Not only does every employee have access to the right suite of tools for their role, but their access is often managed at the group or role level rather than individually, reducing the workload on your IT pros.
2) Security
Traditional security regularly has one point of disappointment the password. If a user’s password gets exposed or, more awful, the email address for their sensitive data recoveries, your company becomes more vulnerable to threat actors. Identity and Access Management services eliminate potential points of failure and provide tools to support them and spot errors as they happen.
How Does IAM Work?
Identity management solutions often accomplish two things:
1) IAM checks the user’s credentials against a database to authenticate that the user, software, or hardware is who they claim to be. As a result, IAM cloud identity tools are more versatile and secure than traditional username and password systems.
2) Identity access management systems only permit access at the proper level. For instance, IAM technology enables portioned access to specific software parts, such as editor, viewer, and commenter in a content management system, rather than granting login and password access to a complete software suite.
What Does IAM Do?
IAM solutions offer this core functionality.
| Tasks | Services |
| Single sign on | Thanks to identity and access management solutions with single sign on (SSO), users can authenticate their identities with one portal rather than numerous resources. In addition, the user no longer needs to remember multiple passwords because the IAM system serves as the identity source truth for the various services available after authentication. |
| Provisioning users | Provisioning identifies the tools and access levels (editor, viewer, administrator) needed to access a user. IAM testing tools enable IT departments to provision users by role, department, or other groupings in collaboration with their management. |
| Authorizing users | Access management tools ensure that users receive the precise type and level of tool access to which they are entitled. Users can also be divided into groups or roles so that many users in a cohort can have the same privileges. |
| Manage user identities | IAM systems can integrate with one or more other directories and synchronize with them, or they can be the only directory used to add, modify, and delete users. Users who require specific access to a company’s resources can also create new identities with the help of identity and access management solutions. |
| Authenticating users | IAM configuration verifies a user’s identity by ensuring they are who they claim to be. The current secure authentication standards use adaptive and multi factor authentication (MFA). |
| Reporting | To maintain compliance and evaluate security threats, IAM tools create reports following most operations performed on the platform (such as login time, systems access, and type of authentication). |
Does IAM Improve Regulatory Compliance?

Laws, rules, and contracts all pertain to security. Data security is strictly regulated by data protection laws, including the General Data Protection Regulation (GDPR) in Europe, HIPAA, and the Sarbanes Oxley Act in the United States. With IAM Compliance and IAM security, organizations can ensure that the highest standards of security, tracking, and administrative transparency are maintained, while users and systems consistently meet regulatory and compliance requirements in daily operations.
What are the Benefits of IAM?
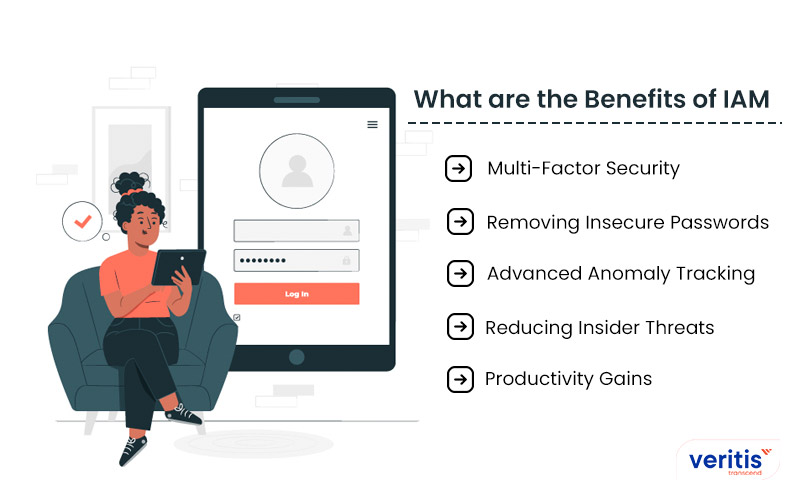
IAM technology can automate the creation, capturing, managing, and administrating of user identities and associated access rights. The five primary benefits of IAM are:
1) Multi Factor Security
IAM best practices assist businesses in transitioning from two factor to three factor authentication, using features such as iris scanning, fingerprint sensors, and facial recognition.
2) Removing Insecure Passwords
According to surveys, weak passwords, defaults, or stolen accounts are responsible for over 80% of data breaches. Identity and access management (IAM) systems enforce the best solutions and prevent users from using default or weak passwords. They also make certain users regularly change their passwords.
3) Advanced Anomaly Tracking
Modern IAM solutions use machine learning, artificial intelligence, and risk based authentication technologies to detect and stop anomalous activity. These go beyond simple credential management.
4) Reducing Insider Threats
Insiders cause an increasing number of breaches. IAM security can prevent malicious insiders from doing further harm by limiting user access to the systems they require to perform their tasks and preventing them from escalating their privileges without monitoring.
5) Productivity Gains
The IAM lifecycle centralizes and automates identity and access management solutions. It establishes automated processes for situations such as new hires and position transitions, which can reduce errors and speed up processing access and identity changes.
Useful link: IAM Implementation and Solutions to Emerging ‘IT Security Challenges’
How Do IAM Technologies and Tools Work?
IAM trends and technologies are built to make account setup and user provisioning easy. With a controlled workflow that eliminates errors and the possibility of misuse while enabling automated account fulfillment, these technologies should decrease the time it takes to perform these tasks. In addition, admins should be able to rapidly view and modify changing access roles and permissions with an IAM best practices system.
These systems should balance the efficiency and automation of their operations with the administrative control required to track and modify access rights. Consequently, the central directory requires an access rights system to manage access requests that automatically associate employee job titles and business unit identities with their proper privilege levels.
Let’s look at the most common IAM technologies and tools that today’s companies use.
IAM Technologies
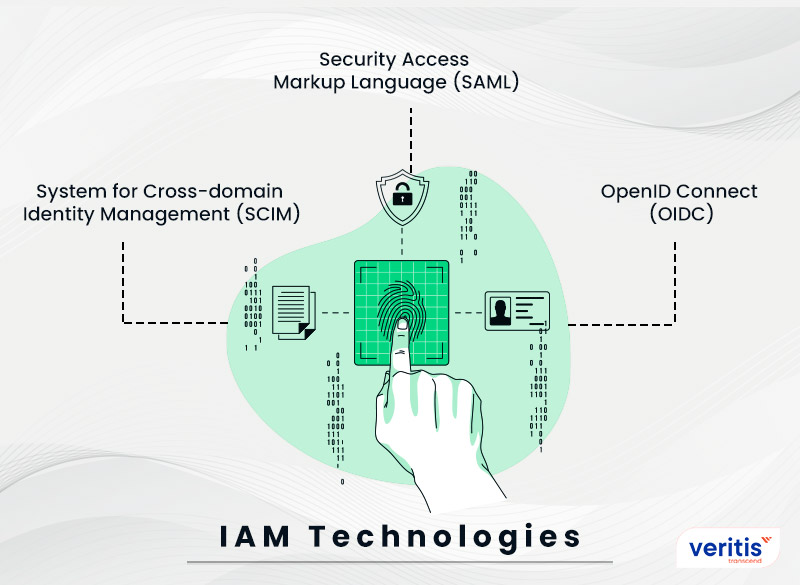
- System for Cross domain Identity Management (SCIM)
- Security Access Markup Language (SAML)
- OpenID Connect (OIDC)
1) System for Cross Domain Identity Management (SCIM)
SCIM is a standard method for automatically exchanging identification data between two systems. Throughout the authentication process, applications can receive identity management system information from SAML and OIDC. SCIM is used to maintain user information up to date when new users are added to the application or service, user data is updated, or users are removed. SCIM is an essential element of user provisioning in the IAM environment.
2) Security Access Markup Language (SAML)
A service or application and an identity provider system, such as IAM trends, can communicate authentication and authorization data using the open standard known as SAML. This is the regular process for IAM best practices to allow users to log in to an application combined with the IAM platform.
3) OpenID Connect (OIDC)
With an identity provider, users can log in to their application using the recent open standard OIDC. It is pretty similar to SAML; however, it is based on the OAuth 2.0 standards and transmits data using JSON rather than XML, as SAML does.
IAM Tools
1) Authentication
- Multi factor authentication
- Biometric authentication
- Behavioral authentication
- Risk based authentication
2) Access Management
- Single sign on
- Context aware network access controls
- Password management
- Pre shared keys
3) Administration
- Access request and review
- Workflow management
- Automated provisioning and de provisioning
- Identity lifecycle management
- Privileged account management
- Segregation of duties
4) Other IAM Tools Include
- OneLogin Trusted Experience Platform
- CloudKnox Permissions Management Platform
- Ping Identity Intelligent Identity Platform
- CyberArk
- ForgeRock
- Microsoft Azure Active Directory
- Okta
- SailPoint
Useful link: Top Tools and Security Protocols That Make IAM Successful!
What are the Challenges and Risks of Implementing IAM?
Users must consider five identity and access management challenges and risks when creating an IAM implementation and continuing maintenance procedures. Let’s examine the challenges and risks associated with IAM implementation.
1) User Password Fatigue
Passwords are essential for maintaining and administering online accounts because external threats are common. Public, private, and federal institutions depend on online accounts to conduct business operations. It requires users to create multiple passwords. Users frequently use the same password for several accounts. Therefore, if one is compromised, it is also possible for other accounts to be readily compromised.
2) Multi Factor Authentication
Although multifactor authentication has some potential benefits, it is not user friendly. Government employees and contractors must frequently carry a different access card or RSA token to access numerous networks and systems. Some users view using a webcam when using their RSA tokens because it can be challenging. Although frequently used for high value applications, multifactor authentication is not entirely secure.
3) Cloud Applications
Cloud based apps have increased significantly, allowing for a connected, worldwide workforce. However, it becomes difficult to determine who has access to information when numerous cloud platforms are running.
4) Managing Access for Remote Work
Accessibility through an internet connected device is one of the significant advantages of cloud applications. However, as there are more apps, there are also more URLs and passwords to monitor, and as mobile device use increases, there are more access points to support and manage. Moreover, with future IAM trends, IT organizations must enable access across several devices and platforms without sacrificing security.
5) Multiple Applications for Different Administration Models
As cloud applications become simple and less expensive to set up, organizations are embracing more point SaaS solutions every day. These solutions are frequently managed by the respective functional department in a business, in the case of Salesforce.com, the Sales Operations group. This can help IT because it frees up time and delegates application administration to others.
What is the Difference Between Identity Management and Access Management?

Since so few individuals need to be aware of the differences, identity management, and access management tools are essentially the same. At the very least, they are unaware of the differences between the two concepts. Therefore, although they have a connection, they are different.
- The Identity management portal refers to authenticating users
- Access management refers to authorized users
1) Identity Management
An identity management system handles digital identities, which entail entries and digital attributes in the database that provide a user with a special designation. Its administration involves creating, maintaining, supervising, and deleting such identities as they function within the business network. In addition, companies must ensure users have the permissions necessary to do their tasks and limit unauthorized access. It also manages authentication.
2) Access Management
Meanwhile, access management tools handle user’s decisions on whether they have to allow or block from accessing a database and resources. Moreover, it handles the access portals through protocols and login pages. Instead, it handles authorization.
How to Deploy Your IAM System: Cloud vs. On premises
One of the main factors driving the popularity of cloud services is their quick, simple implementation. On the other hand, with an on premises deployment, you must provide the computers and have someone install the software on them. This takes time, especially in a clustered environment with HA or HP (High Availability or High Performance).
Earlier, a server on an organization’s on premises handled most identity and access management. However, a cloud service provider handles most IAM deployment services, reducing the company’s physical maintenance expenses.
Useful link: IAM Best Practices for Optimal Cloud Security
What is AWS Identity and Access Management?
IAM is the IAM testing tools system integrated into Amazon Web Services (AWS). Using AWS Identity and Access Management (IAM), you can create users and groups and grant them access to AWS services and resources.
AWS IAM offers users free access.
AWS IAM service offers:
- AWS multi factor authentication
- Access control for AWS resources with great precision
- Analysis tools to verify and improve policy
- Combine with external identity management solutions
What Does an IAM Implementation Strategy Include?

An IAM solution should be designed using zero trust principles such as identity based security policies and least privilege access as the cornerstone of a zero trust architecture. The following six steps are the IAM implementation strategies.
1) Zero Trust Policy
A zero trust policy means a company’s IAM testing tools solution constantly monitors and secures its users’ identification and access points. Earlier, companies used the “once you’re in, you have access” policy. However, zero trust rules ensure that every employee is continually recognized and their access is managed.
2) Secure Access
IAM testing tools should verify the identities of users logging in, as identity level security is crucial. This could include implementing MFA and adaptive authentication to evaluate the context of the login attempt, such as location, time, device, and more.
3) Secured Privileged Accounts
An access management system does not treat all accounts equally. To reflect their role as an organization’s gatekeeper, accounts with privileged access to sensitive information or specific tools can be offered security and assistance.
4) Central Identity Management
Zero trust’s primary principle is accessing resources at the identity level. Consequently, centralizing the management of such identities can make this process much more manageable. This can entail transferring users from other platforms or synchronizing your IAM testing tools with other user directories in your culture, such as a directory for human resources.
5) Policy Based Control
Users should not be granted more privileges than necessary; they should only be allowed permission to do their necessary tasks. Users should be granted access to resources through an IAM deployment depending on their department, job role, or other relevant qualities. The centrally controlled identification solution can then use these policies to secure resources.
6) Training and Support
IAM and CIAM service providers offer training for administrators and users who will be most involved with the product. They frequently provide long term customer support to ensure the health of your identity and access management tools and their users.
Useful link: Regulatory Compliance Made ‘Easier’ With IAM Solutions
Case Study: Services Firm Migrates from SailPoint to Azure AD
Veritis guided a large professional services firm through a phased migration from on premises SailPoint to Azure Active Directory, synchronizing users and groups, automating access workflows with Azure Automation and PowerShell, and enforcing Conditional Access and MFA. This transition reduced licensing and infrastructure costs by over 50%, decreased IAM support effort by 30%, and strengthened security posture with native Azure controls. Most importantly, it achieved full audit ready compliance with zero downtime, ensuring the project’s success.
Read the complete case study: Successful Migration of a Services Firm from SailPoint to Azure AD.
Conclusion
IAM is an important project for any business. It is becoming more business aligned and demands business skills, not just technical experts. Enterprises with well developed identity and access management tools capabilities can lower their identity management portal system expenses while significantly increasing their agility in supporting new business initiatives.
But most significantly, the hosting environment must be one of the primary deciding elements when selecting an IAM solution. Your options will ultimately depend on your specific business, IT needs, and the user base (internal/external, IoT device, etc.) you want to support. This is where Veritis steps in.
Veritis, the Stevie Awards winner, has extensive knowledge and expertise in implementing complicated IT projects and integrating new technology in a dynamic environment. Dynamic, scalable, resilient, and responsive products ensure rapid growth and excellent value for our clients. So, approach us to embrace productivity with the most excellent IAM tools.
Schedule a Call with Our IAM Expert
Additional Resources:
- Best Practices for Effective IAM Implementation
- Robust Identity Management With ‘8 Point IAM Audit Checklist’ and ‘IAM Strategy’
- Healthcare Identity and Access Management (IAM): Five Steps to Transformation
- 5 Reasons Why Financial Sector Needs Identity and Access Management (IAM)
- Identity and Access Management Trends for 2025
- What to Expect: Future Trends in Identity and Access Management